DES Network. Computer and Network Examples
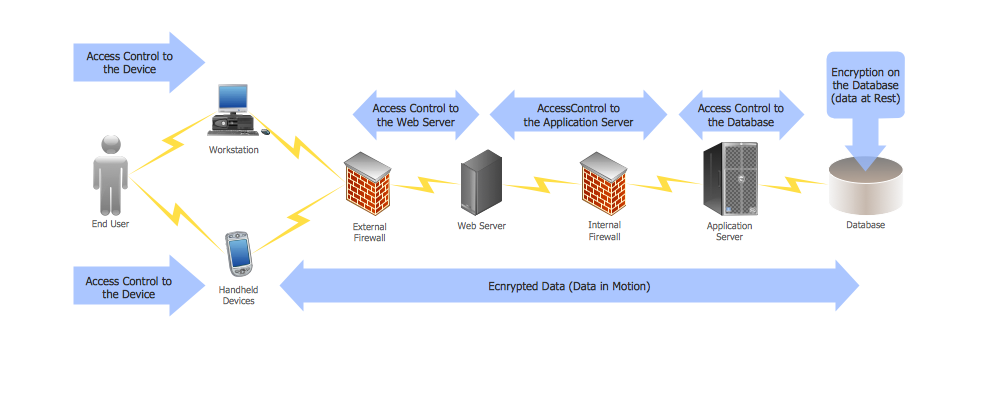
The Data Encryption Standard (DES) is a symmetric-key algorithm for the encryption of the electronic data.
The encryption is an important issue for any organization, it allows to safely keep, handle and transmit the sensitive data through the local network, wireless network or the Internet. The encryption applies the key to the plain text and converts it into the ciphertext. The ciphertext at that looks like the set of the random characters.
The key is a mathematical algorithm known only to the sender and the recipient of the message. The applying of the key to the ciphertext will convert it back to the plain text - it is the decryption process.
This diagram was created in ConceptDraw DIAGRAM using the Computer and Networks Area of ConceptDraw Solution Park and shows how the encryption and access control work together to secure data.
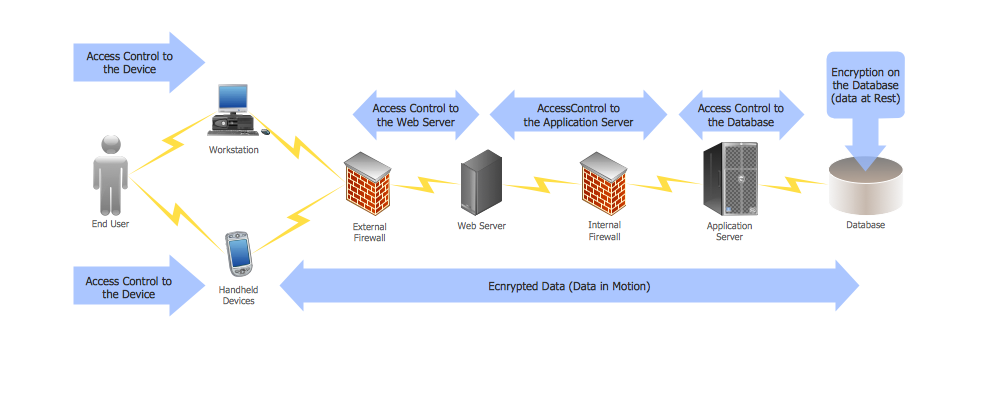
Example 1. DES network.
Using the solutions of the Computer and Networks Area for ConceptDraw DIAGRAM you can create your own computer network diagrams quick and easy.
The diagrams designed with ConceptDraw DIAGRAM are vector graphic documents and are available for reviewing, modifying, and converting to a variety of formats (image, HTML, PDF file, MS PowerPoint Presentation, Adobe Flash or MS Visio).
See also Samples:
EIGHT RELATED HOW TO's:
The Internet is a huge world with unlimited possibilities. But with all its numerous advantages, the Internet also conceals many dangers and security threats, that's why we advise you to follow simple network security tips. ConceptDraw DIAGRAM diagramming and vector drawing software supplied with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park is an ideal software for easy designing Network Security Diagrams and attractive illustrations with effective network security tips.
Picture: Network Security Tips
Related Solution:
An example flowchart of marketing analysis shows main steps you have to challenge writing a marketing analysis.
Picture: Flowchart Example: Flow Chart of Marketing Analysis
Related Solution:
ConceptDraw software has been developed for drawing any type of flowchart. Use RapidDraw - thi is flowchart maker technology for adding new objects to a flowchart quickly. This is technology of fast drawing technique focused on making great-looking flowcharts quickly. To get started using it download flowchart maker ConceptDraw DIAGRAM.
Picture: Flowchart Program Mac
Related Solution:
The Value Stream Mapping solution continues to extend the range of ConceptDraw DIAGRAM into a business graphics tool that can be used to document processes of Lean Manufacturing.
Picture: Lean Manufacturing Diagrams
Related Solution:
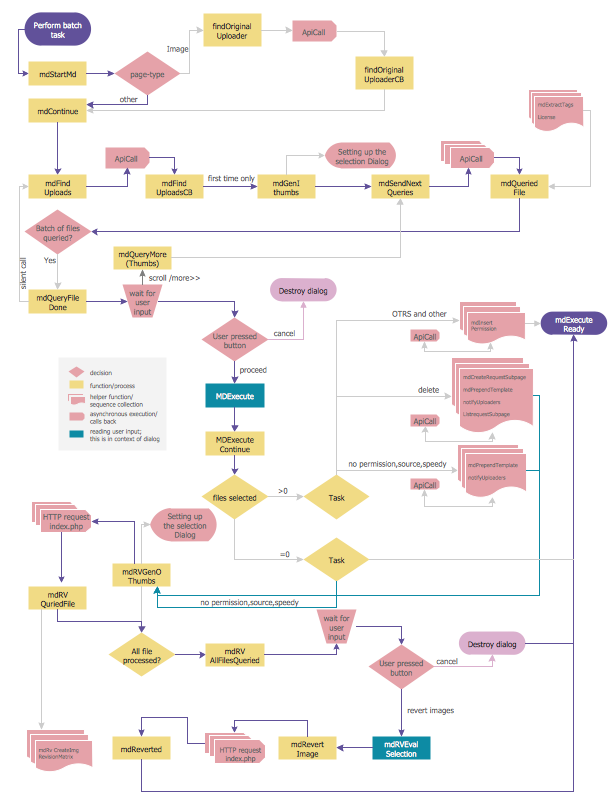
Flowcharts can be used in designing and documenting both simple and complex processes or programs and, similar to the other types of diagrams, they can help visualize what happens and so help understand some definite process, and, as a result, find flaws, bottlenecks and other features within it.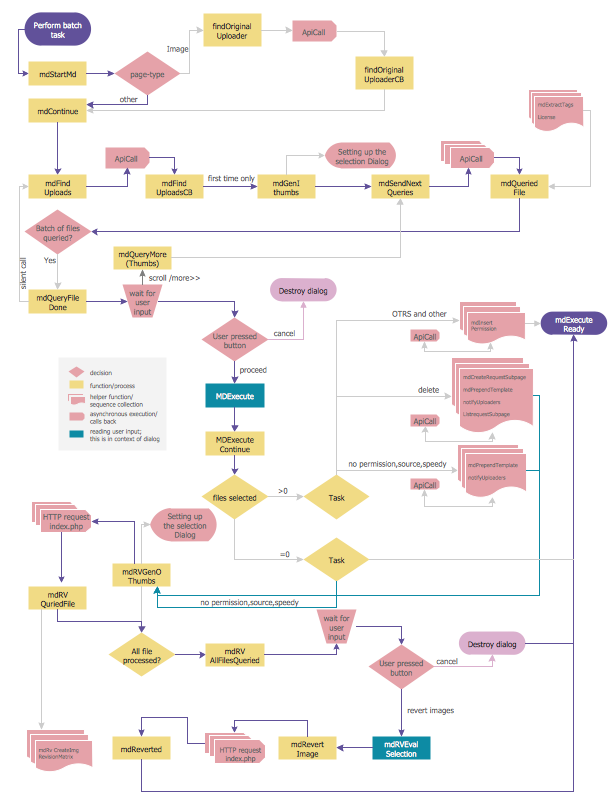
Picture: Flowchart Programming Project. Flowchart Examples
Related Solution:
Create professional business process diagrams using ConceptDraw Activities library with 34 objects from BPMN.
Picture: Business Process Model and Notation Elements: Activities
A Home Area Networks (HAN) is a type of local area network that is used in an individual home. The home computers can be connected together by twisted pair or by a wireless network. HAN facilitates the communication and interoperability among digital devices at the home, allows to easier access to the entertainments and increase the productivity, organize the home security.
This example was created in ConceptDraw DIAGRAM using the Computer and Networks Area of ConceptDraw Solution Park and shows the home network diagram.
Picture: Home area networks (HAN). Computer and Network Examples
Related Solution:
Creation of well thought-out network security model will effectively help you in realization your network's security. ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park lets fast and easy design all variety of network security models: Open network security model, Closed network security model, Restrictive network access model.
Picture: Network Security Model
Related Solution: