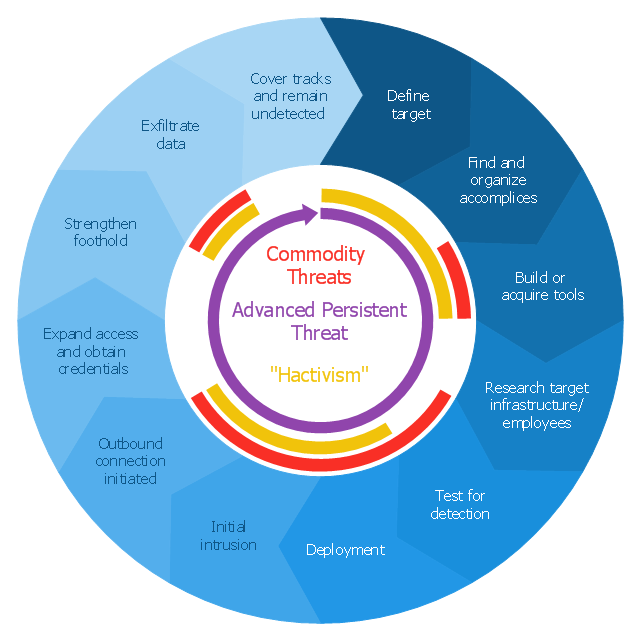
This circular arrows diagram sample shows advanced persistent threat lifecycle.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
How to Help Customers be More Productive
Presenting you with a drawing program which could really surprise you with their great functionality. Don't know how to start to draw Connector's improvement? Curious how should diagramming software work? Drawing programs involve a lot of things like designs in an illustrative way, creating an cherts, Tools to create high end graphics, create dashboards, using your data and many other technical aspects do it in a much professional and in a quick way.- Flow Chart For Extraction Of The Three Components System
- Basic Flowchart Symbols and Meaning | Process Flowchart | Data ...
- Flow Chart On Food Components
- Circular Arrows Diagrams | Systems development life cycle ...
- Flow Chart On Components Of Food
- Diagram Of Marketing Information System
- Design elements - Education charts | How to Draw a Scatter ...
- Program to Make Flow Chart | Innovation life cycle - Arrow loop ...
- Pyramid Diagram | Pyramid Chart Examples | Pyramid Diagram ...
- Pie Chart Examples and Templates | Donut Chart Templates ...
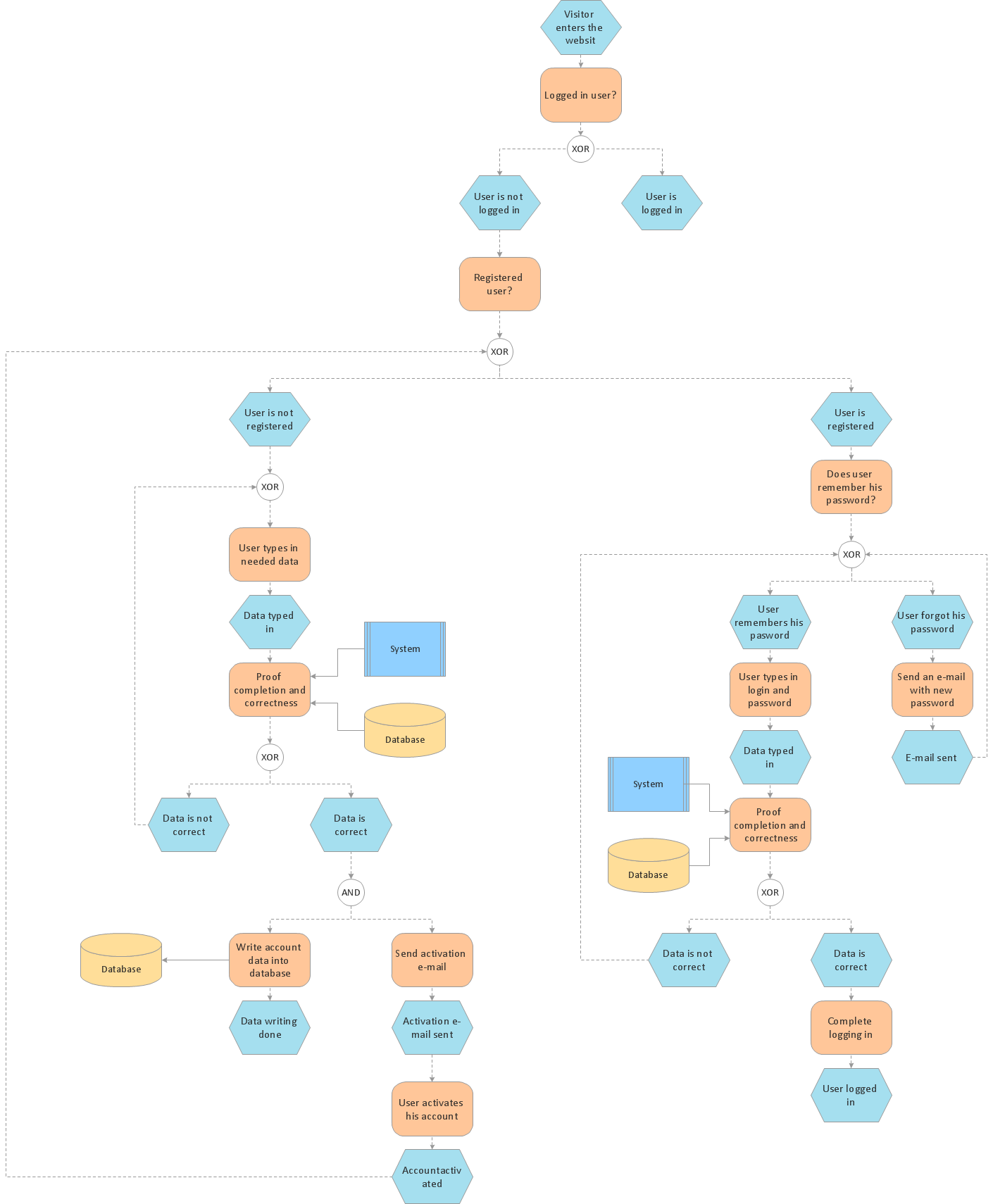
- Account Flowchart Stockbridge System . Flowchart Examples | Data ...
- Pyramid Diagram | Pyramid Diagram | Pyramid Diagram ...
- Pyramid Diagram | Pyramid Diagram | Pyramid Diagram | Data ...
- Pyramid Diagram | Pyramid Diagram | Pyramid Diagram ...
- Pyramid Diagram | Types of Flowcharts | Types of Flowchart ...
- Flowchart design. Flowchart symbols, shapes, stencils and icons ...
- Grid Network Topology | Grid computing system architecture ...
- How to Draw a Circular Arrows Diagram Using ConceptDraw PRO ...
- Process Flowchart | How to Draw an Organization Chart ...
- Advanced persistent threat lifecycle | Creatively Draw A Diagram ...