How to Create a Column Chart
The question how to create a column chart have a simple answer. Use ConceptDraw tips to find out how to create a column chart depicts your data the best way.Column Chart Examples
Column chart examples from ConceptDraw collection can help you find the best visual depiction for you data. You can easily modify column chart examples according to data you want to visualize.
 Bar Graphs
Bar Graphs
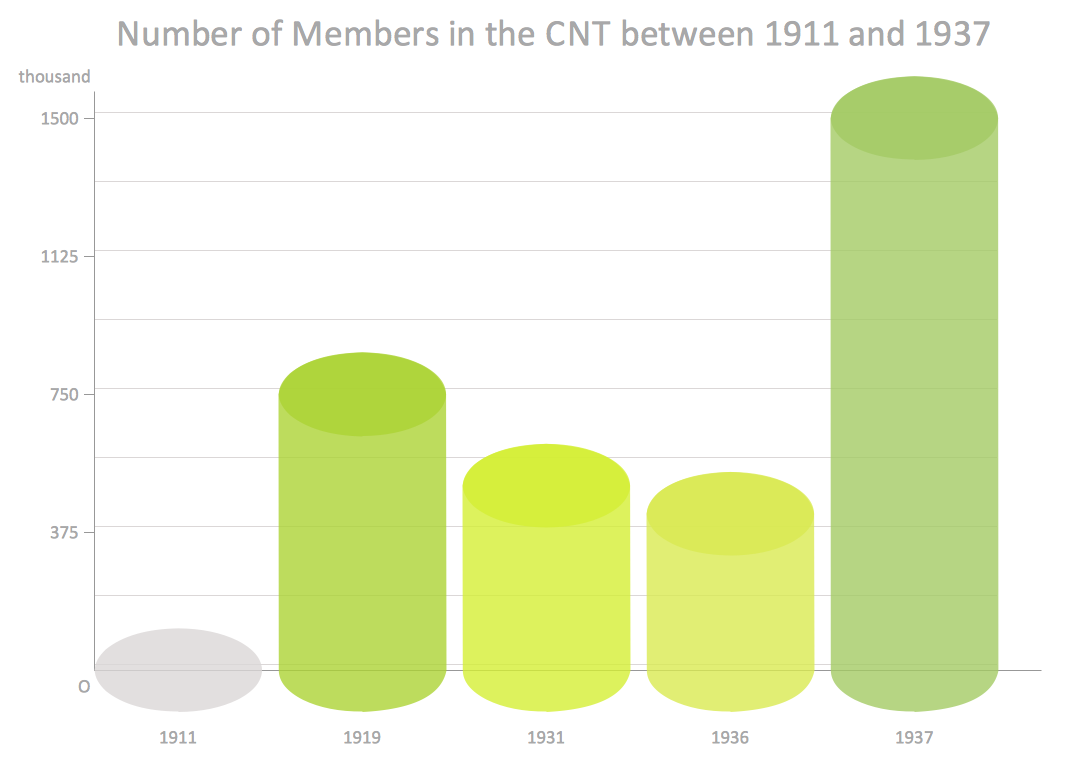
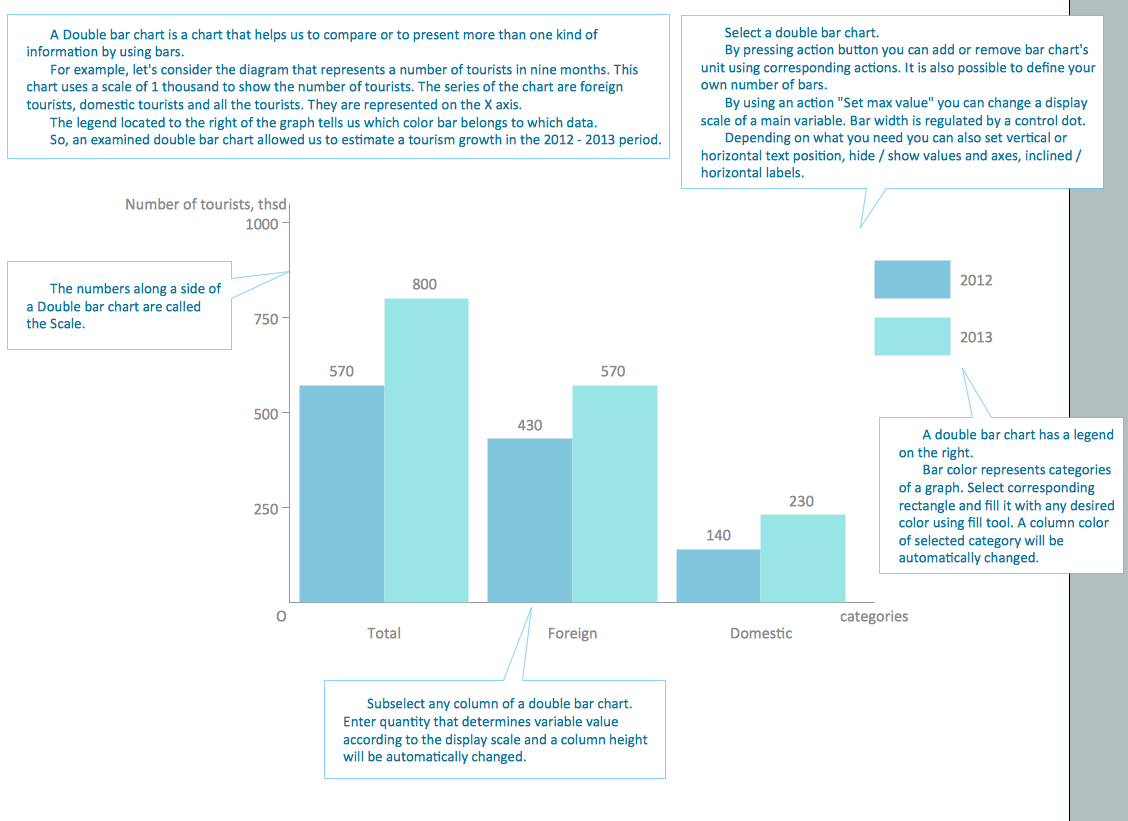
The Bar Graphs solution enhances ConceptDraw PRO v10 functionality with templates, numerous professional-looking samples, and a library of vector stencils for drawing different types of Bar Graphs, such as Simple Bar Graph, Double Bar Graph, Divided Bar Graph, Horizontal Bar Graph, Vertical Bar Graph, and Column Bar Chart.
Chart Examples
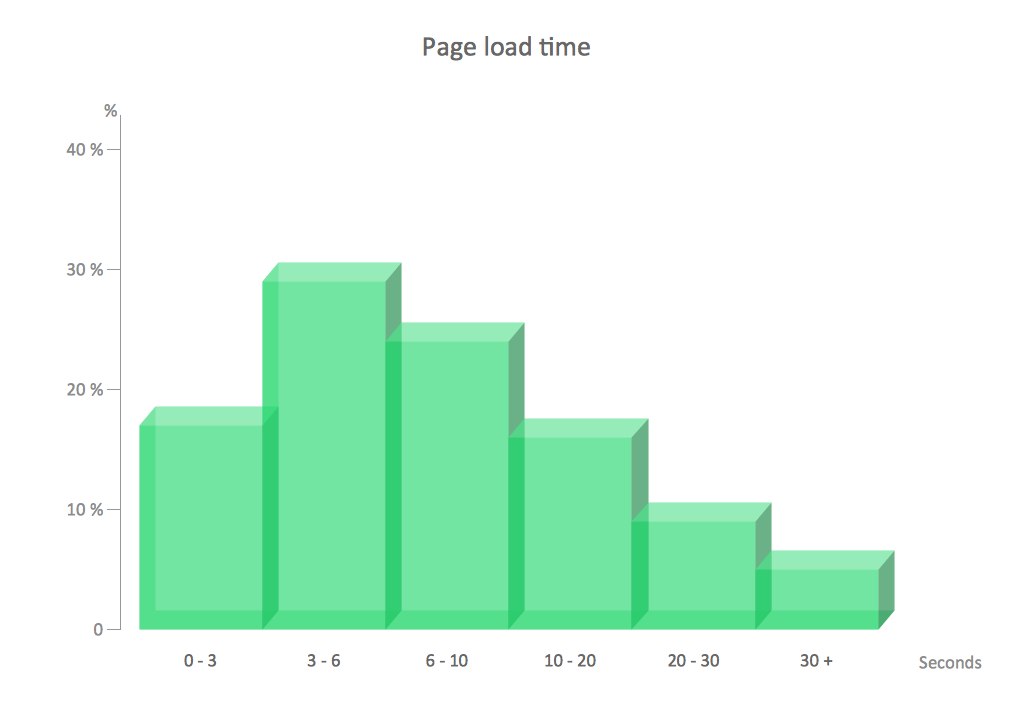
Easy charting software comes with beautiful chart templates and examples. This makes it easy to create professional charts without prior experience.Chart Templates
Easy charting software comes with beautiful chart templates and examples. This makes it easy to create professional charts without prior experience.Column Chart Template
Column chart templates from ConceptDraw collection can help you find the best visual depiction for you data. You can easily modify column chart templates according to data you want to visualize.Virtual private networks (VPN). Computer and Network Examples
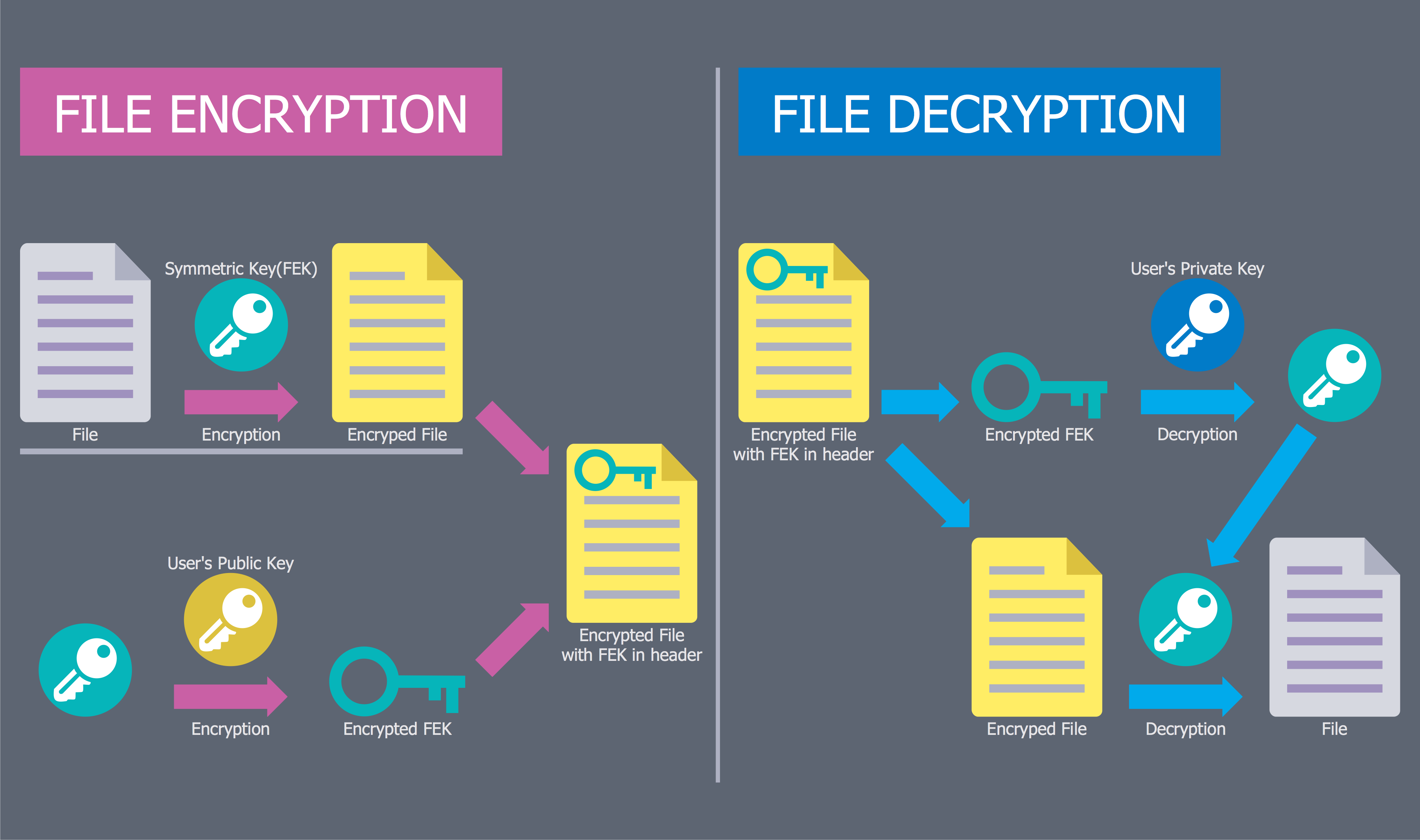
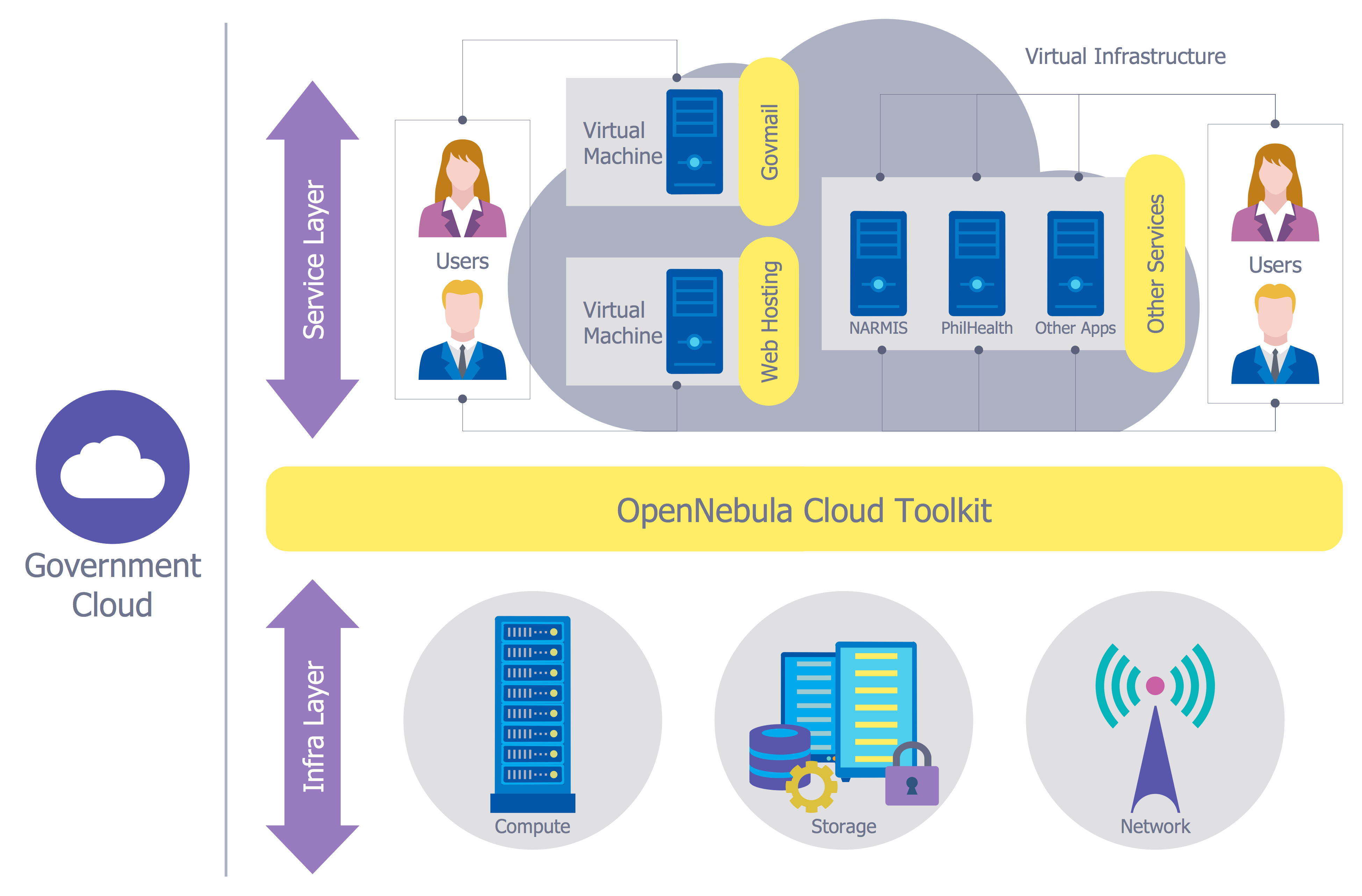
A Virtual Private Network (VPN) is a network that allows the private networks at a remote location securely connect to the public Internet and provide access only to the intended recipients for transmitting data. VPN is built by creating the virtual point-to-point connection using the dedicated connections, traffic encryption or virtual tunneling protocols.This example was created in ConceptDraw PRO using the Computer and Networks Area of ConceptDraw Solution Park and shows the Virtual Private Network (VPN) diagram.
Network Security Diagram
ConceptDraw PRO diagramming and vector drawing software enhanced with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park is the best for effective design professional, colorful and attractive Network Security Diagram of any complexity and degree of detailing.Physical Security Plan
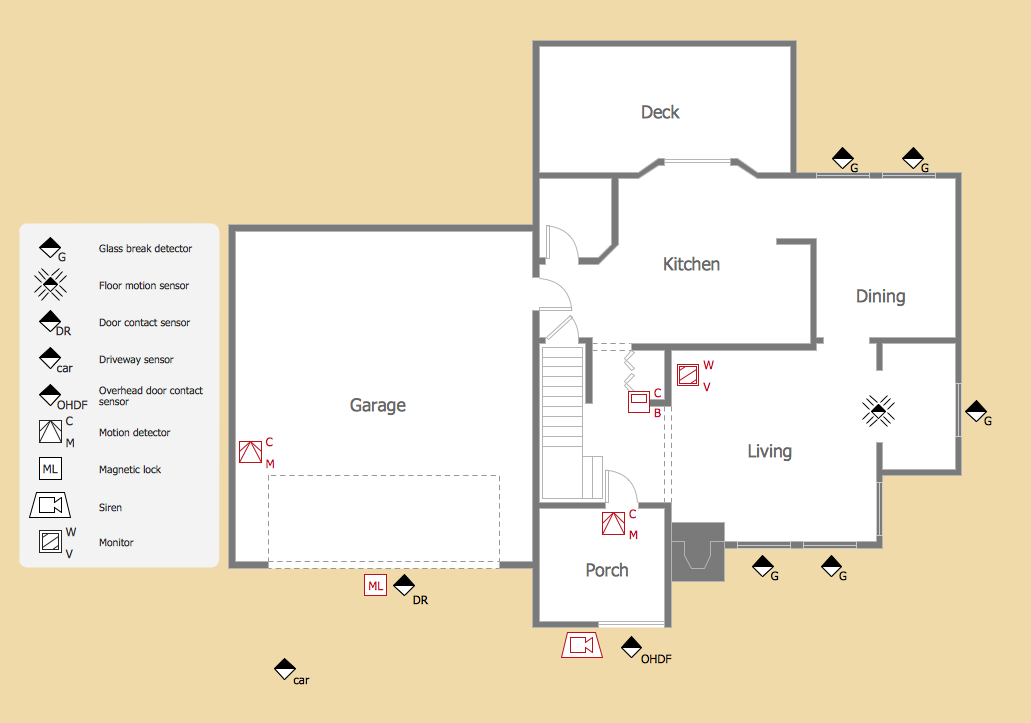
ConceptDraw PRO diagramming and vector drawing software extended with Security and Access Plans Solution from the Building Plans Area of ConceptDraw Solution Park is a powerful software for fast and easy drawing professional looking Physical Security Plan.Cisco Security. Cisco icons, shapes, stencils and symbols
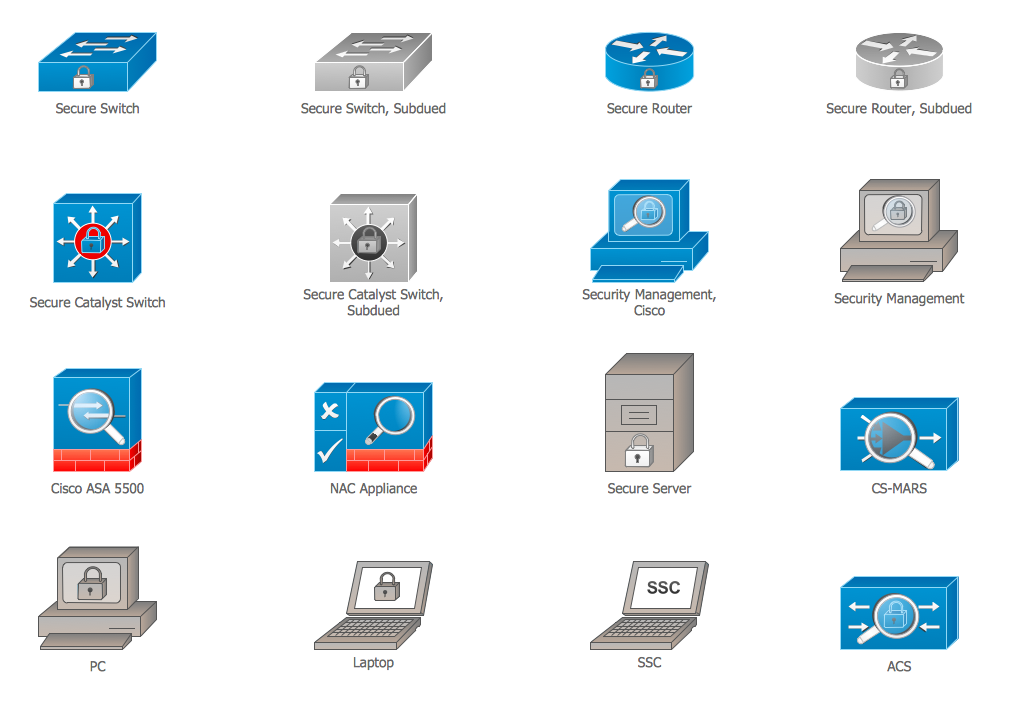
The ConceptDraw vector stencils library "Cisco Security" contains 16 symbols of security devices and equipment for drawing the computer network diagrams using the ConceptDraw PRO diagramming and vector drawing software.Network Security
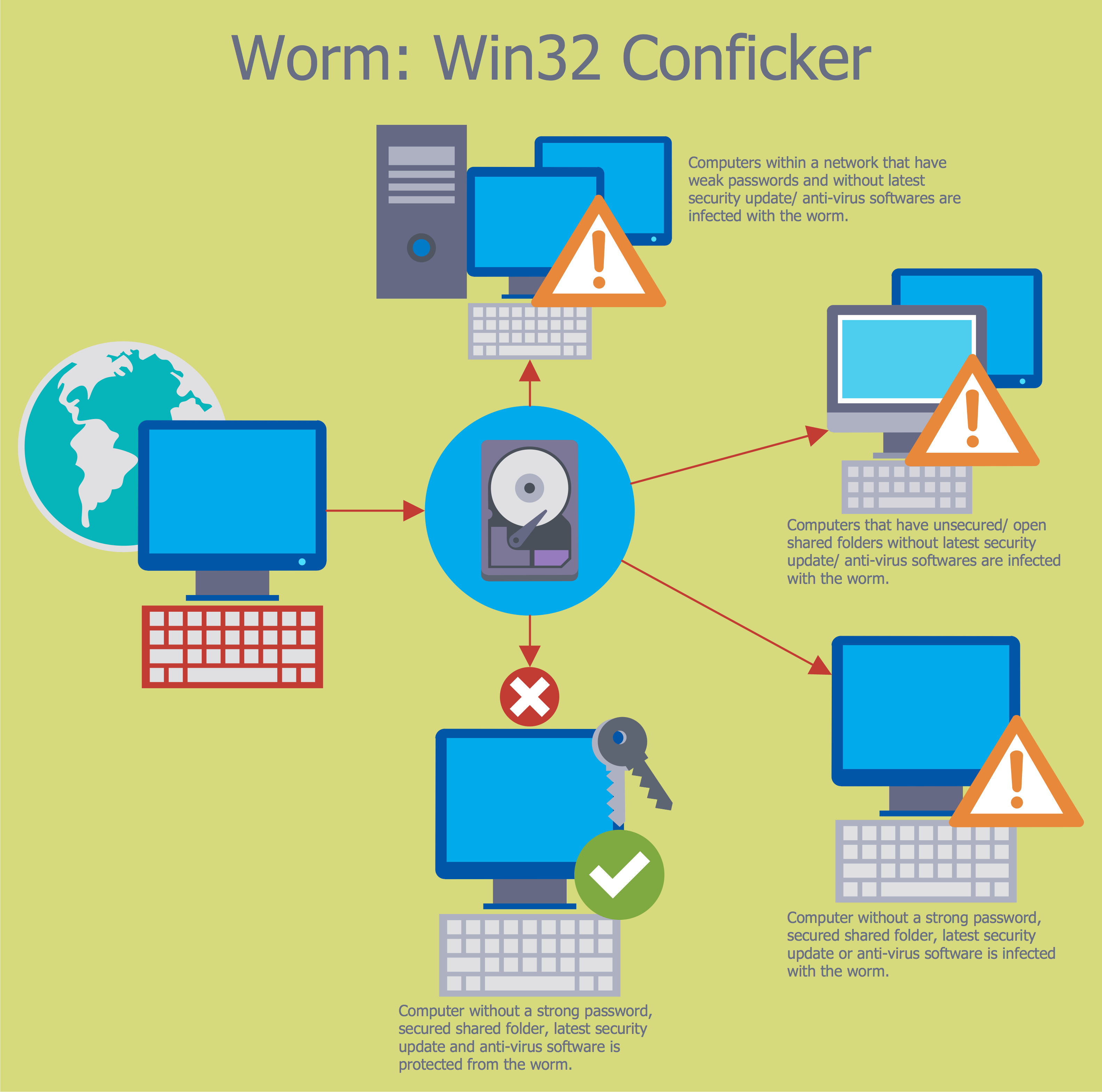
The Internet is a giant computer network which connects computers all over the world. It is integral part of human society and business. But the serious question for network engineers, designers, lawmakers and enforcers is the need for protect the Internet networks from the Internet crimes, hacking and attacks. There are quite a number of hardware, software and physical methods of protection against them.The samples you see on this page were created in ConceptDraw PRO using the tools of Network Security Diagrams Solution for ConceptDraw PRO software. They show protection networks with Firewalls and other network security devices.
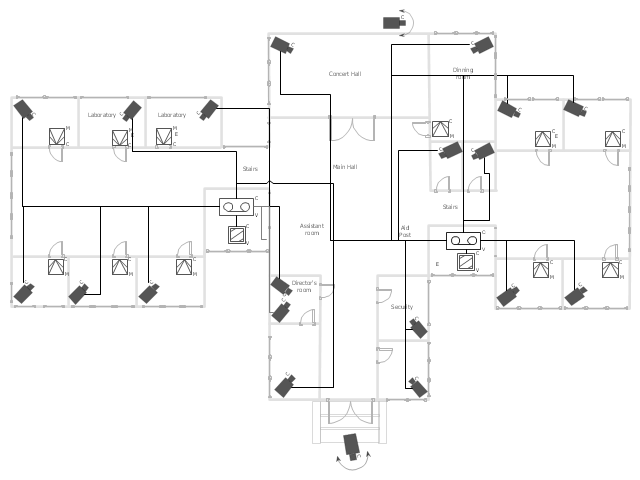
"Closed-circuit television (CCTV) is the use of video cameras to transmit a signal to a specific place, on a limited set of monitors. It differs from broadcast television in that the signal is not openly transmitted, though it may employ point to point (P2P), point to multipoint, or mesh wireless links. Though almost all video cameras fit this definition, the term is most often applied to those used for surveillance in areas that may need monitoring such as banks, casinos, airports, military installations, and convenience stores. Videotelephony is seldom called "CCTV" but the use of video in distance education, where it is an important tool, is often so called.
In industrial plants, CCTV equipment may be used to observe parts of a process from a central control room, for example when the environment is not suitable for humans. CCTV systems may operate continuously or only as required to monitor a particular event. A more advanced form of CCTV, utilizing digital video recorders (DVRs), provides recording for possibly many years, with a variety of quality and performance options and extra features (such as motion detection and email alerts). More recently, decentralized IP cameras, some equipped with megapixel sensors, support recording directly to network-attached storage devices, or internal flash for completely stand-alone operation. Surveillance of the public using CCTV is particularly common in many areas around the world. In recent years, the use of body worn video cameras has been introduced as a new form of surveillance. ... In the United States, closed-circuit television is used for school security to monitor visitors, track unacceptable student behavior and maintain a record of evidence in the event of a crime. There are some restrictions on installation, cameras may not be used in an area where there is a "reasonable expectation of privacy". Examples of these are bathrooms, gym locker areas and private offices (unless consent by the office owner is given). Сameras are generally acceptable in hallways, parking lots, front offices where students, employees, and parents come and go, gymnasiums, cafeterias, supply rooms and classrooms. The use of cameras in classrooms is often debated by teachers who want cameras for protection and teachers who do not." [Closed-circuit television. Wikipedia]
The floor plan example "Video surveillance scheme" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Security and Access Plans solution from the Building Plans area of ConceptDraw Solution Park.
In industrial plants, CCTV equipment may be used to observe parts of a process from a central control room, for example when the environment is not suitable for humans. CCTV systems may operate continuously or only as required to monitor a particular event. A more advanced form of CCTV, utilizing digital video recorders (DVRs), provides recording for possibly many years, with a variety of quality and performance options and extra features (such as motion detection and email alerts). More recently, decentralized IP cameras, some equipped with megapixel sensors, support recording directly to network-attached storage devices, or internal flash for completely stand-alone operation. Surveillance of the public using CCTV is particularly common in many areas around the world. In recent years, the use of body worn video cameras has been introduced as a new form of surveillance. ... In the United States, closed-circuit television is used for school security to monitor visitors, track unacceptable student behavior and maintain a record of evidence in the event of a crime. There are some restrictions on installation, cameras may not be used in an area where there is a "reasonable expectation of privacy". Examples of these are bathrooms, gym locker areas and private offices (unless consent by the office owner is given). Сameras are generally acceptable in hallways, parking lots, front offices where students, employees, and parents come and go, gymnasiums, cafeterias, supply rooms and classrooms. The use of cameras in classrooms is often debated by teachers who want cameras for protection and teachers who do not." [Closed-circuit television. Wikipedia]
The floor plan example "Video surveillance scheme" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Security and Access Plans solution from the Building Plans area of ConceptDraw Solution Park.
Network Security Model
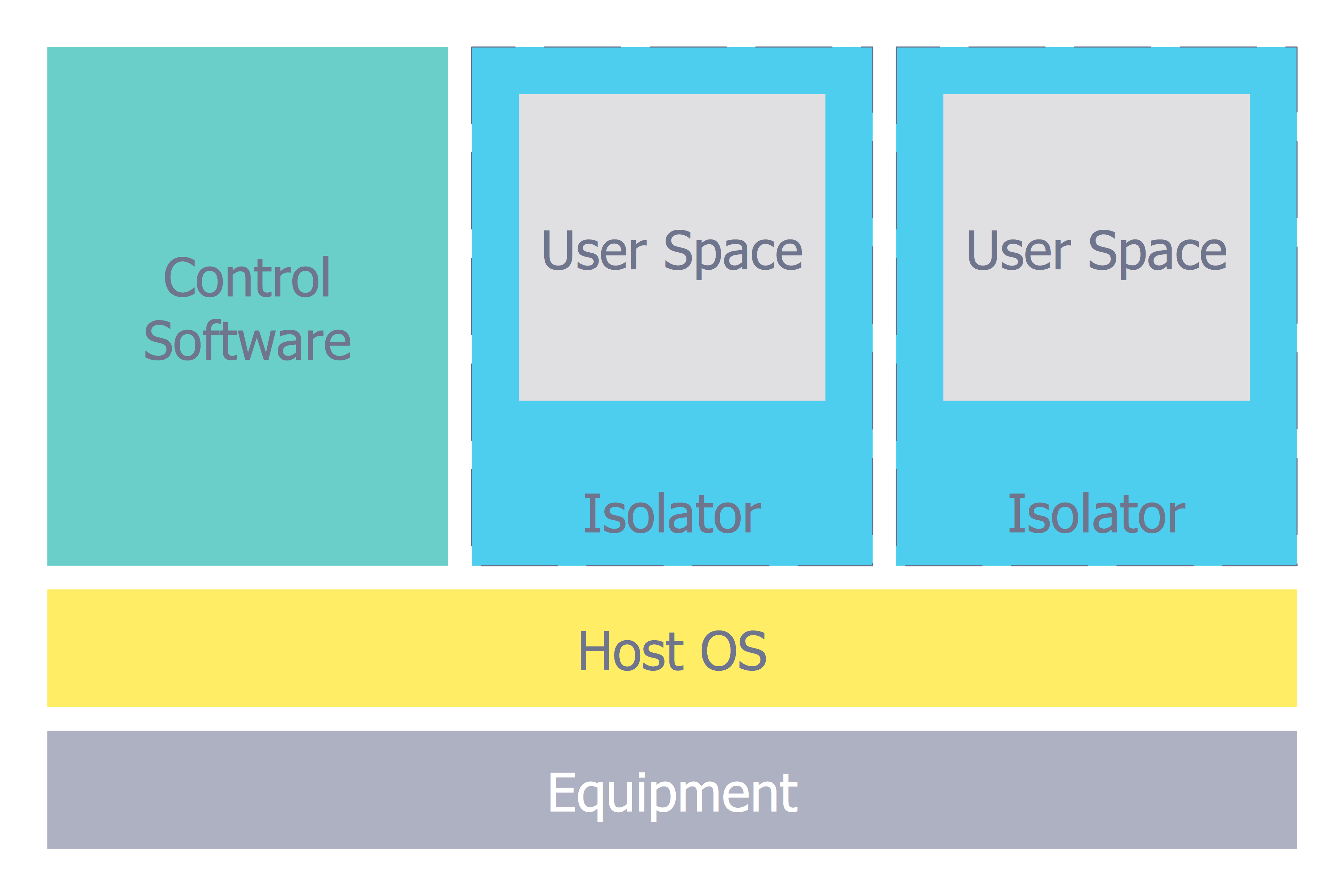
Creation of well thought-out network security model will effectively help you in realization your network's security. ConceptDraw PRO diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park lets fast and easy design all variety of network security models: Open network security model, Closed network security model, Restrictive network access model.Network Security Tips
The Internet is a huge world with unlimited possibilities. But with all its numerous advantages, the Internet also conceals many dangers and security threats, that's why we advise you to follow simple network security tips. ConceptDraw PRO diagramming and vector drawing software supplied with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park is an ideal software for easy designing Network Security Diagrams and attractive illustrations with effective network security tips.Network Security Architecture Diagram
Network Security Architecture Diagram visually reflects the network's structure and construction, and all actions undertaken for ensuring the network security which can be executed with help of software resources and hardware devices. You dream to find powerful software for easy designing Network Security Architecture Diagram? We recommend to use ConceptDraw PRO extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park.- A Flow Diagram Of Crime Solution Processes
- Crime Solution Processes Flow Diagram
- Flow Diagram Of Solving Crimes In Communities
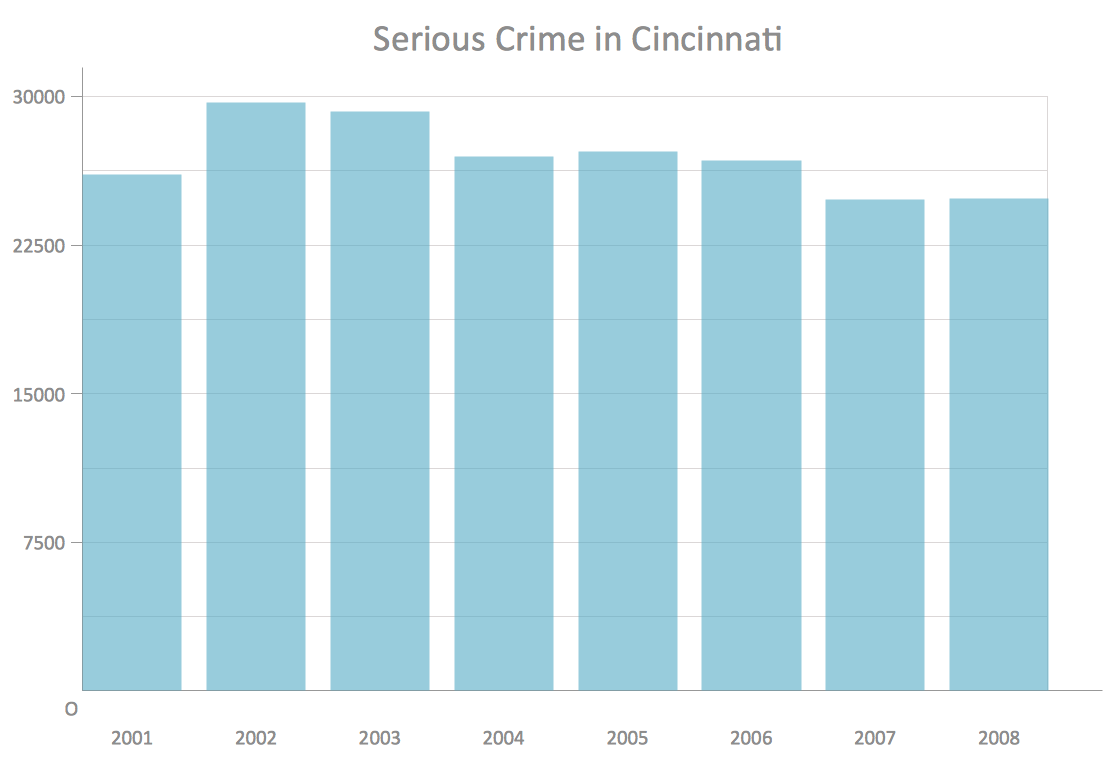
- Bar graph - Serious Crime in Cincinnati | How to Create a Column ...
- Building Plans Area | Business Process Diagrams | Security and ...
- Bar Chart Examples | Sales Growth. Bar Graphs Example | Financial ...
- Draw A Flow Diagram Of Ways To Solve A Crime
- How to Create a Column Chart | How to Create a Line Chart | How to ...
- London election results - Divided bar diagram | Pie Chart Software ...
- Event-driven Process Chain (EPC) Diagrams | Food security ...
- Bar graph - Serious Crime in Cincinnati | Column Chart Examples ...
- Process Flowchart | Flow chart Example. Warehouse Flowchart ...
- Pictures Of Flow Diagram Of Way To Solve Crime Problem
- Network Security Diagrams | How to Create a Network Security ...
- Process Flowchart | Network Security | Campus Area Networks ...
- Business process diagram BPMN 1.2 - Hiring process | Process ...
- | Process Flowchart | Mind Map Exchange | Hardware Mind Map
- Www Bar Graph Representing Crime
- Network Security | Cisco Security. Cisco icons, shapes, stencils and ...
- Process Flowchart | Pyramid Diagram | Pyramid Diagram | Definition ...