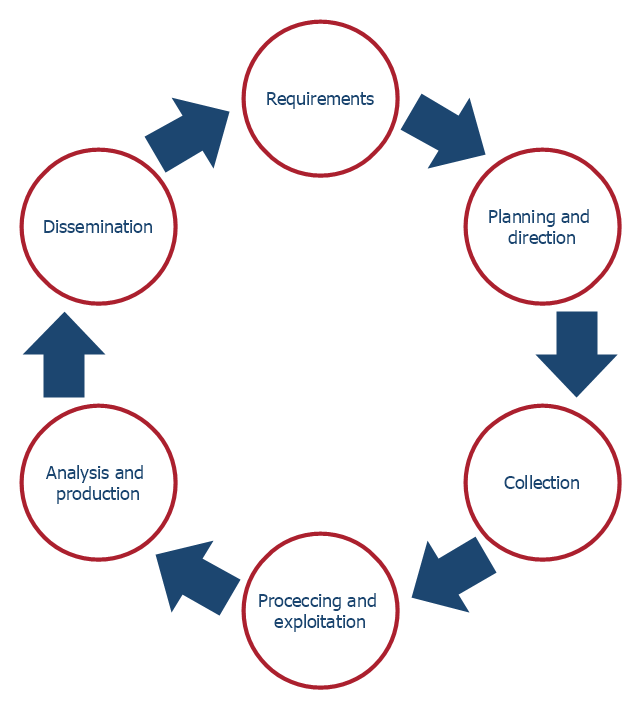
This arrow loop diagram sample was created on the base of the figure illustrating the article "Up Close and Personal. Life as an Intelligence Analyst" from the FBI website. [fbi.gov/ news/ stories/ 2006/ may/ arias050506]
"The traditional Intelligence cycle is the fundamental cycle of intelligence processing in a civilian or military intelligence agency or in law enforcement as a closed path consisting of repeating nodes. The stages of the intelligence cycle include the issuance of requirements by decision makers, collection, processing, analysis, and publication of intelligence. The circuit is completed when decision makers provide feedback and revised requirements. The intelligence cycle is also called the Intelligence Process by the U.S. Department of Defense (DoD) and the uniformed services." [Intelligence cycle. Wikipedia]
The arrow loop diagram example "Intelligence analyst cycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Target and Circular Diagrams solution from the Marketing area of ConceptDraw Solution Park.
www.conceptdraw.com/ solution-park/ marketing-target-and-circular-diagrams
"The traditional Intelligence cycle is the fundamental cycle of intelligence processing in a civilian or military intelligence agency or in law enforcement as a closed path consisting of repeating nodes. The stages of the intelligence cycle include the issuance of requirements by decision makers, collection, processing, analysis, and publication of intelligence. The circuit is completed when decision makers provide feedback and revised requirements. The intelligence cycle is also called the Intelligence Process by the U.S. Department of Defense (DoD) and the uniformed services." [Intelligence cycle. Wikipedia]
The arrow loop diagram example "Intelligence analyst cycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Target and Circular Diagrams solution from the Marketing area of ConceptDraw Solution Park.
www.conceptdraw.com/ solution-park/ marketing-target-and-circular-diagrams
 Target and Circular Diagrams
Target and Circular Diagrams
This solution extends ConceptDraw PRO software with samples, templates and library of design elements for drawing the Target and Circular Diagrams.
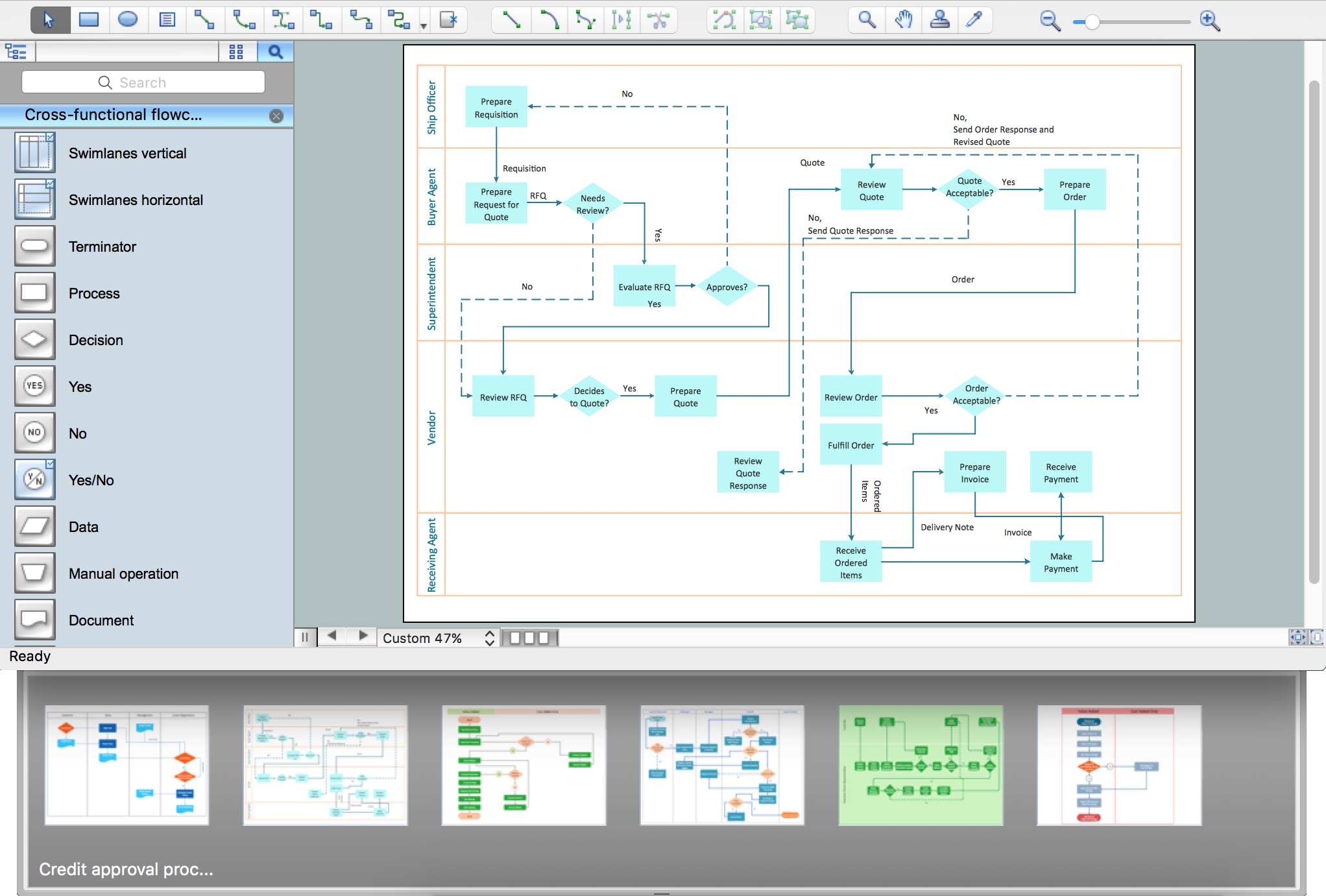
Process Flowchart
The main reason of using Process Flowchart or PFD is to show relations between major parts of the system. Process Flowcharts are used in process engineering and chemical industry where there is a requirement of depicting relationships between major components only and not include minor parts. Process Flowcharts for single unit or multiple units differ in their structure and implementation. ConceptDraw PRO is Professional business process mapping software for making Process flowcharts, Process flow diagram, Workflow diagram, flowcharts and technical illustrations for business documents and also comprehensive visio for mac application. Easier define and document basic work and data flows, financial, production and quality management processes to increase efficiency of your business with ConcepDraw PRO. Business process mapping software with Flowchart Maker ConceptDraw PRO includes extensive drawing tools, rich examples and templates, process flowchart symbols and shape libraries, smart connectors that allow you create the flowcharts of complex processes, process flow diagrams, procedures and information exchange. Process Flowchart Solution is project management workflow tools which is part ConceptDraw Project marketing project management software. Drawing charts, diagrams, and network layouts has long been the monopoly of Microsoft Visio, making Mac users to struggle when needing such visio alternative like visio for mac, it requires only to view features, make a minor edit to, or print a diagram or chart. Thankfully to MS Visio alternative like ConceptDraw PRO software, this is cross-platform charting and business process management tool, now visio alternative for making sort of visio diagram is not a problem anymore however many people still name it business process visio tools.
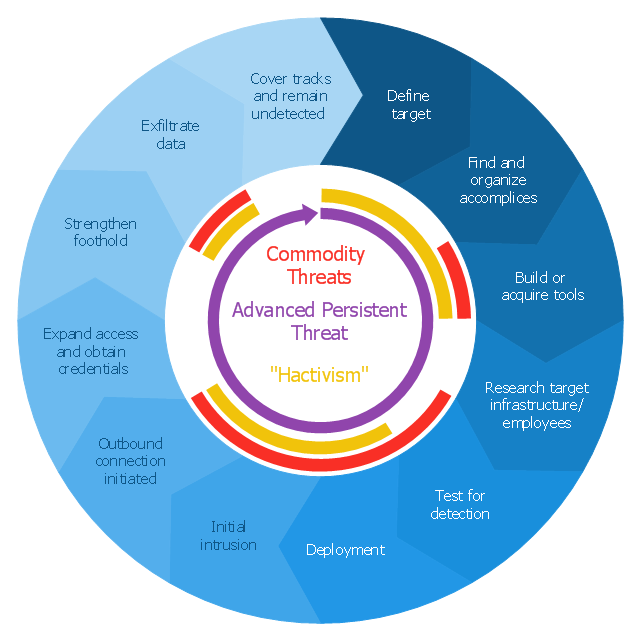
Circular Diagram
Circular Diagram is a type of diagram widely used in marketing and economics for visualization information in a clear and visual form. ConceptDraw PRO diagramming and vector drawing software offers the useful tools of the Target and Circular Diagrams solution from the Marketing area of ConceptDraw Solution Park for effective drawing a Circular Diagram of any complexity and design.This circular arrows diagram sample shows advanced persistent threat lifecycle.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
- Intelligence analyst cycle - Arrow loop diagram | The Circular Flow ...
- Intelligence analyst cycle - Arrow loop diagram | Target and Circular ...
- Stakeholder Onion Diagrams | Rapid UML | Intelligence analyst ...
- Product life cycle process - Flowchart | Intelligence analyst cycle ...
- Last resort hotel book room process - DFD | Intelligence analyst ...
- Product life cycle process - Flowchart | Circular Arrows Diagrams ...
- Innovation life cycle - Arrow loop diagram | National Preparedness ...
- Proton-proton chain reaction diagram | Water cycle diagram ...
- Water cycle diagram | Circular arrows diagram - PDCA cycle ...
- Business feedback loop | Innovation life cycle - Arrow loop diagram ...
- Innovation life cycle - Arrow loop diagram
- Intelligence analyst cycle - Arrow loop diagram
- Process Flowchart | Schematic Diagram For Social Intelligence
- Process Flowchart | Camera layout schematic | Social Intelligence ...
- Process Flowchart | Camera layout schematic | Schematics Of Social ...
- Process Flowchart | Social Intelligence Schematic Diagram
- Diagram That Indicates Human Life Cycle
- AWS Architecture Diagrams | Process Flowchart | Target and ...
- Process Flowchart | Diagrams Of The Schematic Illustration Of ...
- Process Flowchart | Target and Circular Diagrams | Illustration ...