Process Flowchart
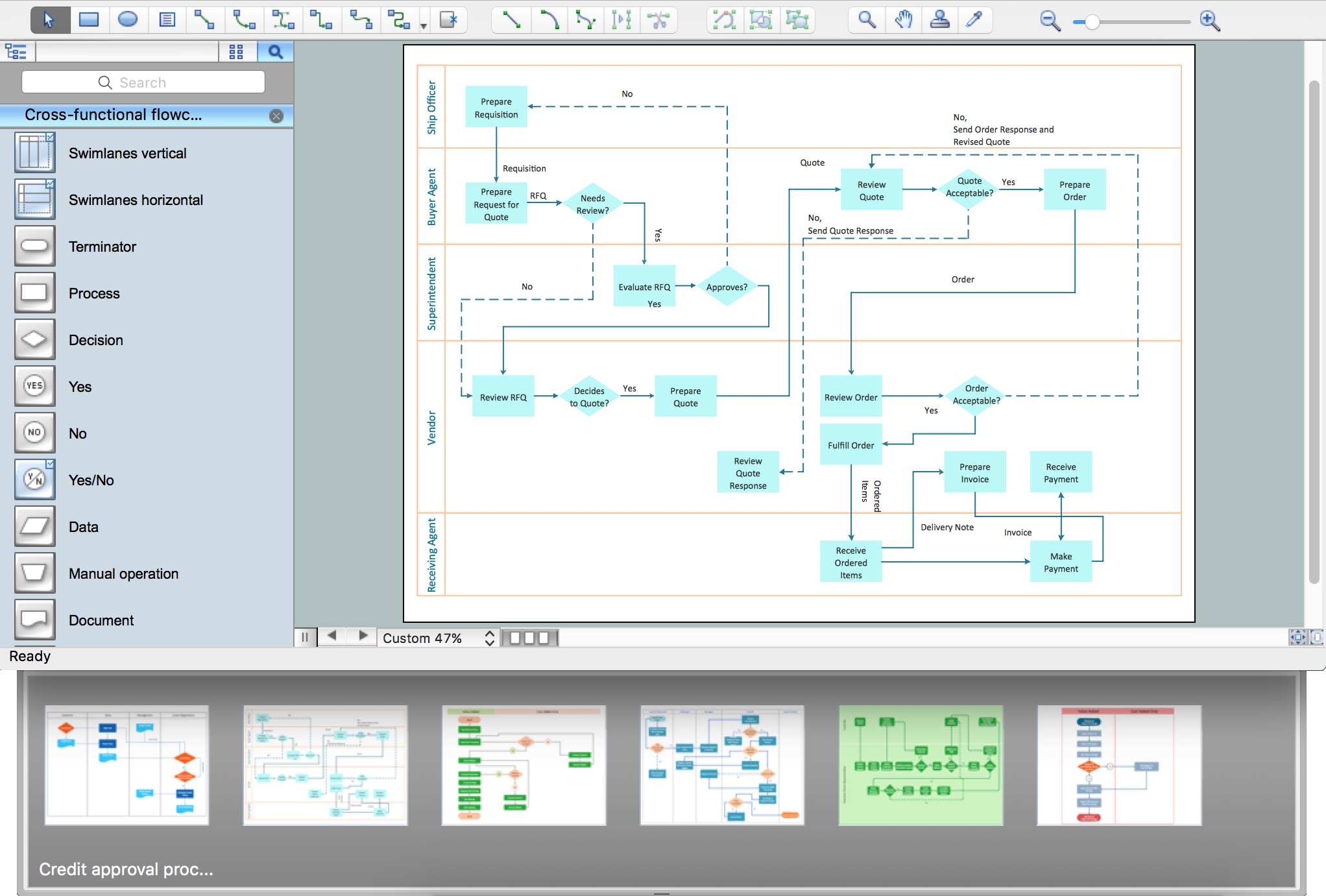
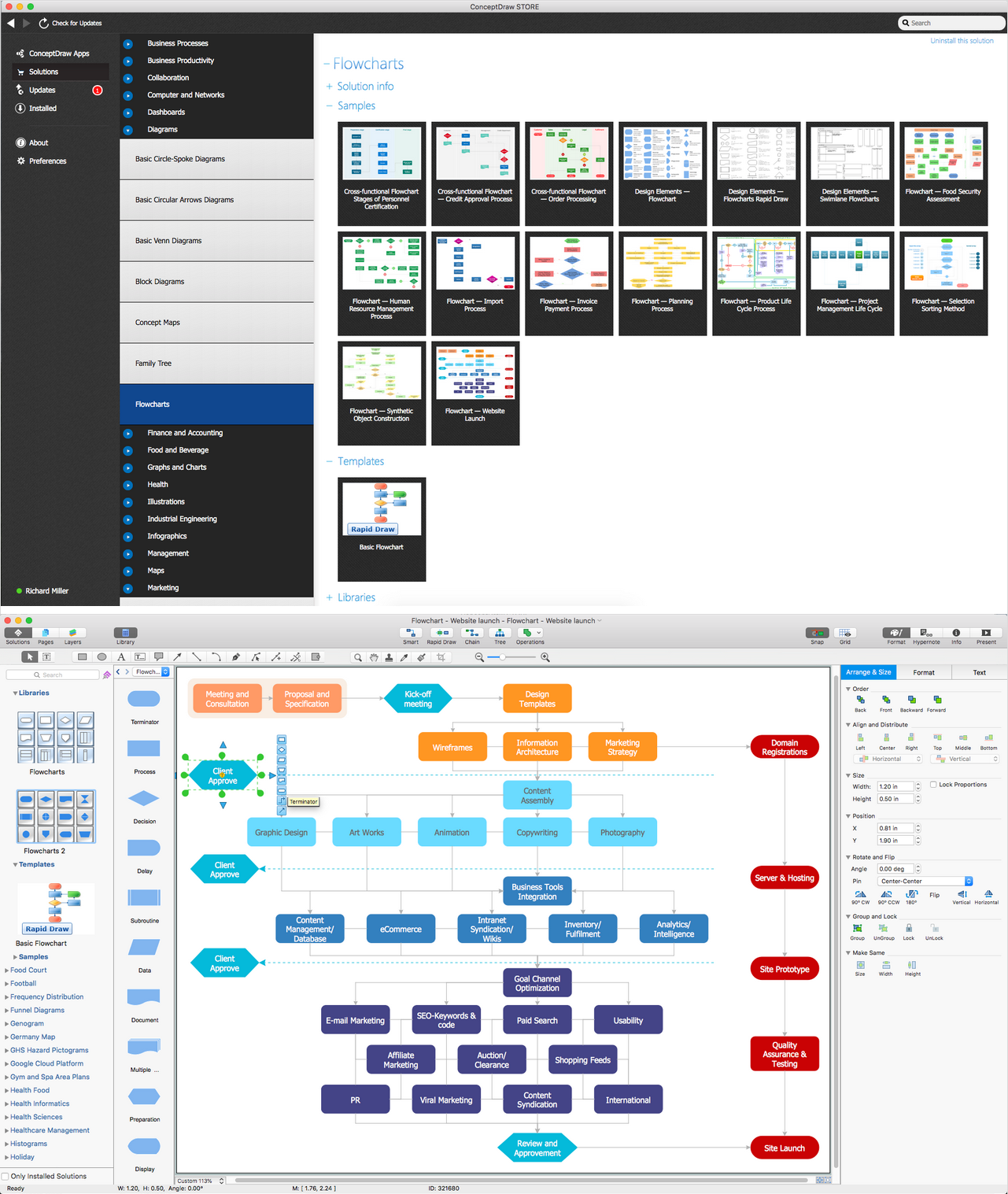
The main reason of using Process Flowchart or PFD is to show relations between major parts of the system. Process Flowcharts are used in process engineering and chemical industry where there is a requirement of depicting relationships between major components only and not include minor parts. Process Flowcharts for single unit or multiple units differ in their structure and implementation. ConceptDraw PRO is Professional business process mapping software for making Process flowcharts, Process flow diagram, Workflow diagram, flowcharts and technical illustrations for business documents and also comprehensive visio for mac application. Easier define and document basic work and data flows, financial, production and quality management processes to increase efficiency of your business with ConcepDraw PRO. Business process mapping software with Flowchart Maker ConceptDraw PRO includes extensive drawing tools, rich examples and templates, process flowchart symbols and shape libraries, smart connectors that allow you create the flowcharts of complex processes, process flow diagrams, procedures and information exchange. Process Flowchart Solution is project management workflow tools which is part ConceptDraw Project marketing project management software. Drawing charts, diagrams, and network layouts has long been the monopoly of Microsoft Visio, making Mac users to struggle when needing such visio alternative like visio for mac, it requires only to view features, make a minor edit to, or print a diagram or chart. Thankfully to MS Visio alternative like ConceptDraw PRO software, this is cross-platform charting and business process management tool, now visio alternative for making sort of visio diagram is not a problem anymore however many people still name it business process visio tools.
Basic Flowchart Symbols and Meaning
Flowcharts are the best for visually representation the business processes and the flow of a custom-order process through various departments within an organization. ConceptDraw PRO diagramming and vector drawing software extended with Flowcharts solution offers the full set of predesigned basic flowchart symbols which are gathered at two libraries: Flowchart and Flowcharts Rapid Draw. Among them are: process, terminator, decision, data, document, display, manual loop, and many other specific symbols. The meaning for each symbol offered by ConceptDraw gives the presentation about their proposed use in professional Flowcharts for business and technical processes, software algorithms, well-developed structures of web sites, Workflow diagrams, Process flow diagram and correlation in developing on-line instructional projects or business process system. Use of ready flow chart symbols in diagrams is incredibly useful - you need simply drag desired from the libraries to your document and arrange them in required order. There are a few serious alternatives to Visio for Mac, one of them is ConceptDraw PRO. It is one of the main contender with the most similar features and capabilities.
 Visio Exchange
Visio Exchange
Our Visio Exchange tool allows you to Import and export native MS Visio 2013 files that are in the new MS Visio drawing (VSDX) format introduced in the most recent Visio iteration. In addition, ConceptDraw PRO v10 supports the import and export of MS Visio 2007-2010 XML. (VDX) files more accurately then previous versions of ConceptDraw PRO. If you have the older MS Visio 2007-2010.
Flow chart Example. Warehouse Flowchart
Warehouse Flowcharts are various diagrams that describe the warehousing and inventory management processes on the warehouses. Typical purposes of Warehouse Flowcharts are evaluating warehouse performance, measuring efficiency of customer service and organizational performance. This type of Workflow diagrams can be used for identifying any disconnection between business activities and business objectives. They are effectively used by warehouse-related people and organizations, manufacturers, wholesalers, exporters, importers, transporters, and others. Standard Warehousing process flow diagram and standard Workflow diagram are used for process identification for further evaluating effectiveness and profitability of overall business process. Use the ConceptDraw PRO vector graphic software extended with Flowcharts solution to design your own professional-looking Workflow diagrams and Flowcharts of any types, including the Warehouse flowchart, Process flow diagrams which depict in details all steps of Warehouse packages flow. Microsoft Visio, designed for Windows users, can’t be opened directly on Mac. But fortunately, there are several Visio alternatives for Mac which will help Mac users to work Visio files. With ConceptDraw PRO, you may open, edit and save files in Visio format.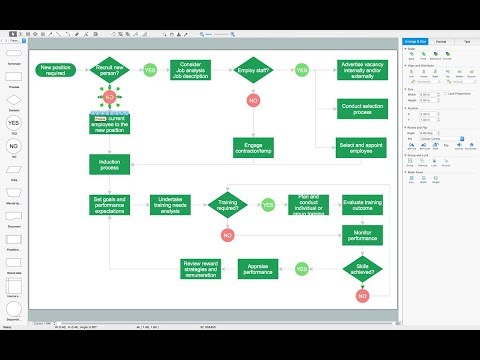
 PM Personal Time Management
PM Personal Time Management
PM Personal Time Management solution extends the ConceptDraw Solution Park and all ConceptDraw Office suite products providing every project participant with tools and features allowing tracking timeframe, workspace and role in a project with the aid of Microreports, calendars, and project To-Do lists. PM Personal Time Management solution makes the collaborative work easier and improves personal performance, now each project participant stays informed about the task lists, calendars and future tasks for itself and its colleagues. Be effective in project management and personal time management, generate easily your personal To-Do lists, personal calendars, personal assignment lists, project checklists, and communicate with your colleagues using e-mail and sending project Microreports via e-mail with one click.
Business Diagram Software
When managing the projects, people, or networks, there are daily designed and used different types of Business diagrams, so the powerful drawing software will be very useful for this. ConceptDraw PRO with large quantity of business solutions will meet your needs and will help you convey your ideas successful and rapidly, no matter are you professional or beginner. It is the best choice for business specialists and technical professionals who need quickly and easily explore, visualize, and communicate information. ConceptDraw PRO business diagram software is the most powerful business software and relational charting software. Create advanced, completely customizable Business Process Diagrams, Business Flow Charts, Work Flow Diagrams, Organizational Charts, Audit diagrams, Marketing diagrams, Value Stream Maps, TQM diagrams, ERD diagrams, EPC diagrams, Cause and Effect diagrams, Infographics, Dashboards, and other Relational business diagrams from your data using the powerful drawing tools of ConceptDraw Solution Park.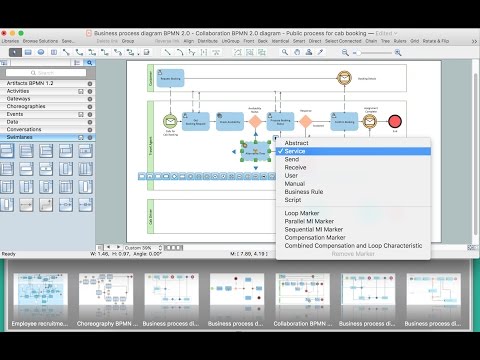
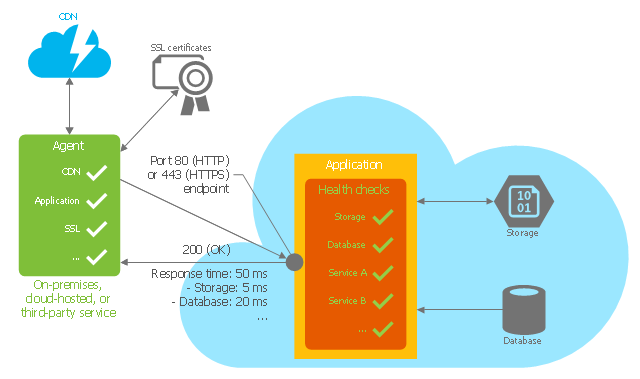
This Azure cloud architecture pattern diagram template was created on the base of figure in the article "Health Endpoint Monitoring Pattern" from the Microsoft Developer Network (MSDN) website.
"Health Endpoint Monitoring Pattern.
Implement functional checks within an application that external tools can access through exposed endpoints at regular intervals. This pattern can help to verify that applications and services are performing correctly. ...
It is good practice—and often a business requirement—to monitor web applications, and middle-tier and shared services, to ensure that they are available and performing correctly. However, it is more difficult to monitor services running in the cloud than it is to monitor on-premises services. ...
Implement health monitoring by sending requests to an endpoint on the application. The application should perform the necessary checks, and return an indication of its status.
A health monitoring check typically combines two factors: the checks (if any) performed by the application or service in response to the request to the health verification endpoint, and analysis of the result by the tool or framework that is performing the health verification check. The response code indicates the status of the application and, optionally, any components or services it uses. The latency or response time check is performed by the monitoring tool or framework." [msdn.microsoft.com/ ru-RU/ library/ dn589789.aspx]
The Azure cloud system architecture diagram template "Health endpoint monitoring pattern" for the ConceptDraw PRO diagramming and vector drawing software is included in the Azure Architecture solutin from the Computer and Networks area of ConceptDraw Solution Park.
"Health Endpoint Monitoring Pattern.
Implement functional checks within an application that external tools can access through exposed endpoints at regular intervals. This pattern can help to verify that applications and services are performing correctly. ...
It is good practice—and often a business requirement—to monitor web applications, and middle-tier and shared services, to ensure that they are available and performing correctly. However, it is more difficult to monitor services running in the cloud than it is to monitor on-premises services. ...
Implement health monitoring by sending requests to an endpoint on the application. The application should perform the necessary checks, and return an indication of its status.
A health monitoring check typically combines two factors: the checks (if any) performed by the application or service in response to the request to the health verification endpoint, and analysis of the result by the tool or framework that is performing the health verification check. The response code indicates the status of the application and, optionally, any components or services it uses. The latency or response time check is performed by the monitoring tool or framework." [msdn.microsoft.com/ ru-RU/ library/ dn589789.aspx]
The Azure cloud system architecture diagram template "Health endpoint monitoring pattern" for the ConceptDraw PRO diagramming and vector drawing software is included in the Azure Architecture solutin from the Computer and Networks area of ConceptDraw Solution Park.
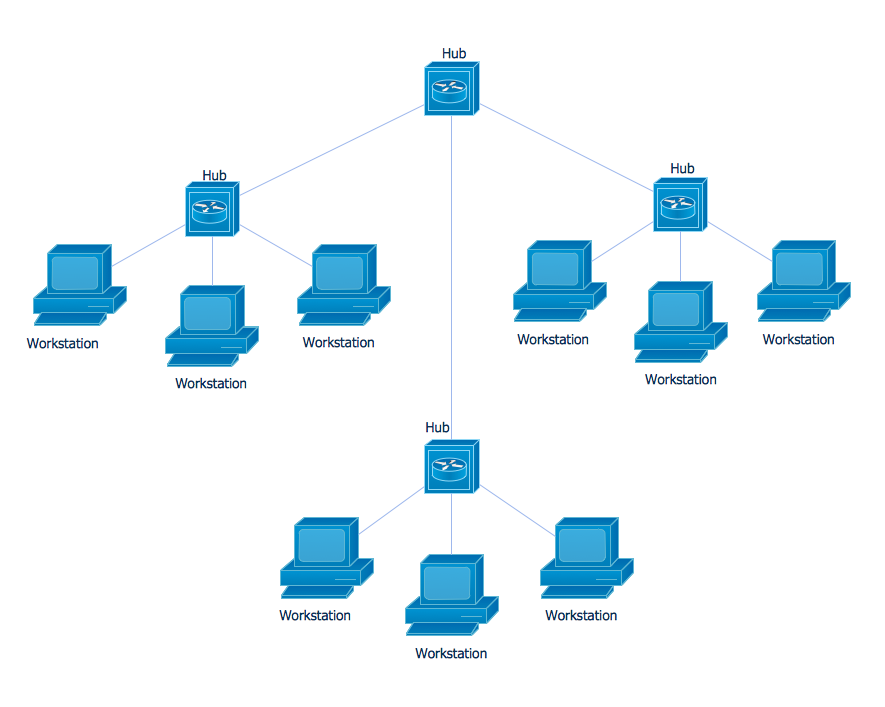
Star Network Topology
Star is a basic computer network topology in which all nodes (computers and peripheral devices) of the network are connected to the central hub or switch with a point-to-point connection, forming a physical network segment. Such network segment can function separately or as a part of complex network topology. The switch is a server, the peripherals are the clients. The large workload and functions of network management are entrusted on the central computer, all information exchange goes through it, so it must to be obligatory the most powerful. The star network topology is a simple topology for design and implementation. Its advantages are high performance, flexible administration capabilities, simplicity of adding additional nodes and search of faults, the fact that a failure of one workstation doesn't affect the work of entire network. But the failure of central hub will result the failure of whole network or network segment - it's the main disadvantage. Use the ConceptDraw PRO with Computer and Networks solution to designing Star Network Topology Diagrams fast and easy.
 Active Directory Diagrams
Active Directory Diagrams
Active Directory Diagrams solution significantly extends the capabilities of ConceptDraw PRO software with special Active Directory samples, convenient template and libraries of Active Directory vector stencils, common icons of sites and services, icons of LDPA elements, which were developed to help you in planning and modelling network structures and network topologies, in designing excellently looking Active Directory diagrams, Active Directory Structure diagrams, and Active Directory Services diagram, which are perfect way to visualize detailed structures of Microsoft Windows networks, Active Directory Domain topology, Active Directory Site topology, Organizational Units (OU), and Exchange Server organization.
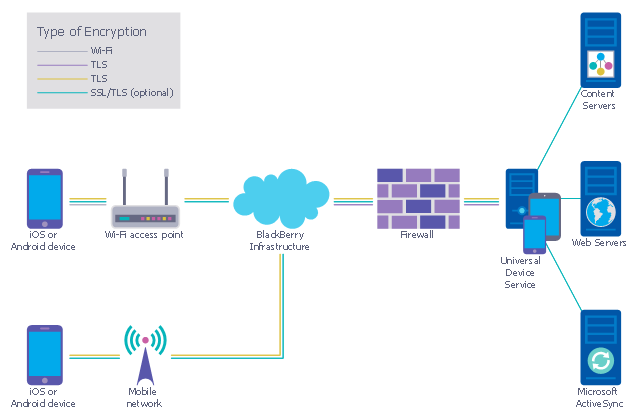
This example was designed on the base of the diagram from the "BYOD Guidance: BlackBerry Secure Work Space" on the website of the UK Communications Electronics Security Group (CESG).
"Secure Work Space (SWS) for iOS and Android is a containerisation, application-wrapping and secure connectivity option that delivers a higher level of control and security to iOS and Android devices, all managed through the BlackBerry Enterprise Service (BES) administration console.
Work space applications are secured and separated from personal applications and data. The work space applications include an integrated email, calendar, and contacts application, an enterprise-level secure browser, and a secure document viewing and editing application.
The work browser allows users to securely browse the organisation’s intranet and the Internet. If the device is lost or the employee leaves the organisation, you can chose to delete only corporate information or all information from the device.
...
Recommended network architecture
The walled garden architecture, shown below, aims to limit the impact of a compromise of an EUD and isolate high risk components from high value components where possible. The enterprise servers installed as part of SWS are high value resources that require suitable protection but are also high risk; they perform complex processing tasks that are more likely to contain exploitable vulnerabilities. These competing priorities make securely placing the servers into an existing network challenging, and organisations that wish to deviate from this architecture below should ensure they understand the risks of doing so."
[cesg.gov.uk/ guidance/ byod-guidance-blackberry-secure-work-space]
The cybersecurity diagram example "Recommended network architecture for BlackBerry SWS" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
"Secure Work Space (SWS) for iOS and Android is a containerisation, application-wrapping and secure connectivity option that delivers a higher level of control and security to iOS and Android devices, all managed through the BlackBerry Enterprise Service (BES) administration console.
Work space applications are secured and separated from personal applications and data. The work space applications include an integrated email, calendar, and contacts application, an enterprise-level secure browser, and a secure document viewing and editing application.
The work browser allows users to securely browse the organisation’s intranet and the Internet. If the device is lost or the employee leaves the organisation, you can chose to delete only corporate information or all information from the device.
...
Recommended network architecture
The walled garden architecture, shown below, aims to limit the impact of a compromise of an EUD and isolate high risk components from high value components where possible. The enterprise servers installed as part of SWS are high value resources that require suitable protection but are also high risk; they perform complex processing tasks that are more likely to contain exploitable vulnerabilities. These competing priorities make securely placing the servers into an existing network challenging, and organisations that wish to deviate from this architecture below should ensure they understand the risks of doing so."
[cesg.gov.uk/ guidance/ byod-guidance-blackberry-secure-work-space]
The cybersecurity diagram example "Recommended network architecture for BlackBerry SWS" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
Simple Flow Chart
ConceptDraw PRO diagramming and vector drawing software extended with Flowcharts Solution from the 'Diagrams' area of ConceptDraw Solution Park is a powerful tool for drawing Flow Charts of any complexity you need. Irrespective of whether you want to draw a Simple Flow Chart or large complex Flow Diagram, you estimate to do it without efforts thanks to the extensive drawing tools of Flowcharts solution, there are professional flowchart symbols and basic flowchart symbols. This sample shows the Gravitational Search Algorithm (GSA) that is the optimization algorithm.- Block Diagram Of Email System
- Block Diagram | Process Flowchart | PM Planning | E Mail Block ...
- Send Email Block Diagram
- Schematic Diagram Of Email
- Block Diagram | Functional Block Diagram | Process Flowchart | E ...
- Block Diagram | Interactive Venn Diagram | Visio Exchange | E Mail ...
- Block Diagram Of E Mail
- Process Flowchart | Block Diagram Of Email Inner Working
- Mail Block Diagram
- Block Diagram | Process Flowchart | Metro Map | E Mail Block Daigram
- Email Concept Block Diagram
- Basic Block Diagram Of Email
- Block Diagram | Campus Area Networks (CAN). Computer and ...
- Block Diagram Of Email
- Process Diagram Of E Mail
- Blocks Diagram Of E Mail
- Structure Of Email Diagram
- Structurr Of Email With Digram
- Email Schematic Diagrams