The vector stencils library "Cybersecurity" contains 24 cybersecurity icons.
Use it to design your computer and telecom illustrations and infographics with ConceptDraw PRO diagramming and vector drawing software.
The vector stencils library "Cybersecurity" is included in the Computers and Communications solution from the Illustration area of ConceptDraw Solution Park.
Use it to design your computer and telecom illustrations and infographics with ConceptDraw PRO diagramming and vector drawing software.
The vector stencils library "Cybersecurity" is included in the Computers and Communications solution from the Illustration area of ConceptDraw Solution Park.
This vector stencils library contains 184 round icons.
Use it to design cloud computing infographics and diagrams with ConceptDraw PRO software.
"Though service-oriented architecture advocates "everything as a service" (with the acronyms EaaS or XaaS or simply aas), cloud-computing providers offer their "services" according to different models, which happen to form a stack: infrastructure-, platform- and software-as-a-service.
Infrastructure as a service (IaaS)
In the most basic cloud-service model ... providers of IaaS offer computers — physical or (more often) virtual machines — and other resources. IaaS refers to online services that abstract the user from the details of infrastructure like physical computing resources, location, data partitioning, scaling, security, backup etc.
Platform as a service (PaaS)
PaaS vendors offer a development environment to application developers. The provider typically develops toolkit and standards for development and channels for distribution and payment. In the PaaS models, cloud providers deliver a computing platform, typically including operating system, programming-language execution environment, database, and web server. Application developers can develop and run their software solutions on a cloud platform without the cost and complexity of buying and managing the underlying hardware and software layers.
Software as a service (SaaS)
In the software as a service (SaaS) model, users gain access to application software and databases. Cloud providers manage the infrastructure and platforms that run the applications. SaaS is sometimes referred to as "on-demand software" and is usually priced on a pay-per-use basis or using a subscription fee.
In the SaaS model, cloud providers install and operate application software in the cloud and cloud users access the software from cloud clients. Cloud users do not manage the cloud infrastructure and platform where the application runs. This eliminates the need to install and run the application on the cloud user's own computers, which simplifies maintenance and support. Cloud applications differ from other applications in their scalability — which can be achieved by cloning tasks onto multiple virtual machines at run-time to meet changing work demand." [Cloud computing. Wikipedia]
The vector stencils library "Cloud round icons" is included in the Cloud Computing Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
Use it to design cloud computing infographics and diagrams with ConceptDraw PRO software.
"Though service-oriented architecture advocates "everything as a service" (with the acronyms EaaS or XaaS or simply aas), cloud-computing providers offer their "services" according to different models, which happen to form a stack: infrastructure-, platform- and software-as-a-service.
Infrastructure as a service (IaaS)
In the most basic cloud-service model ... providers of IaaS offer computers — physical or (more often) virtual machines — and other resources. IaaS refers to online services that abstract the user from the details of infrastructure like physical computing resources, location, data partitioning, scaling, security, backup etc.
Platform as a service (PaaS)
PaaS vendors offer a development environment to application developers. The provider typically develops toolkit and standards for development and channels for distribution and payment. In the PaaS models, cloud providers deliver a computing platform, typically including operating system, programming-language execution environment, database, and web server. Application developers can develop and run their software solutions on a cloud platform without the cost and complexity of buying and managing the underlying hardware and software layers.
Software as a service (SaaS)
In the software as a service (SaaS) model, users gain access to application software and databases. Cloud providers manage the infrastructure and platforms that run the applications. SaaS is sometimes referred to as "on-demand software" and is usually priced on a pay-per-use basis or using a subscription fee.
In the SaaS model, cloud providers install and operate application software in the cloud and cloud users access the software from cloud clients. Cloud users do not manage the cloud infrastructure and platform where the application runs. This eliminates the need to install and run the application on the cloud user's own computers, which simplifies maintenance and support. Cloud applications differ from other applications in their scalability — which can be achieved by cloning tasks onto multiple virtual machines at run-time to meet changing work demand." [Cloud computing. Wikipedia]
The vector stencils library "Cloud round icons" is included in the Cloud Computing Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
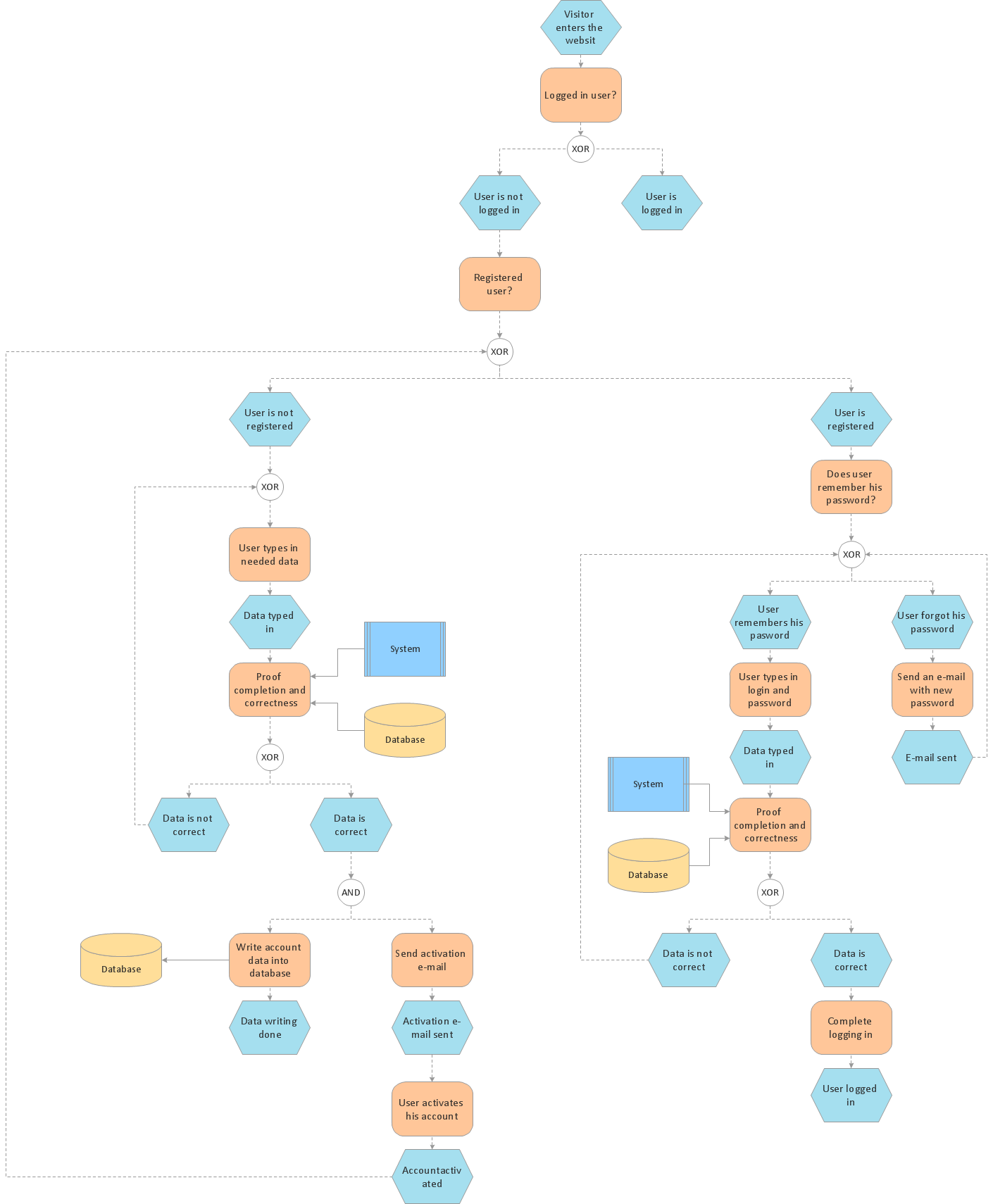
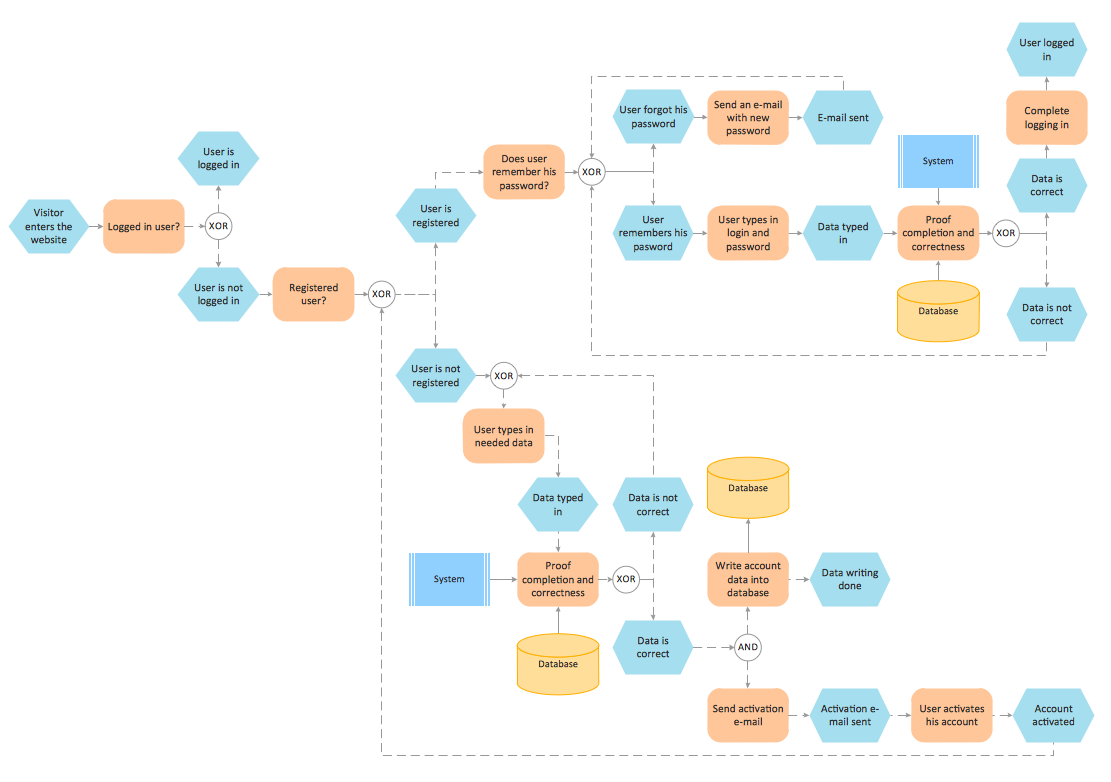
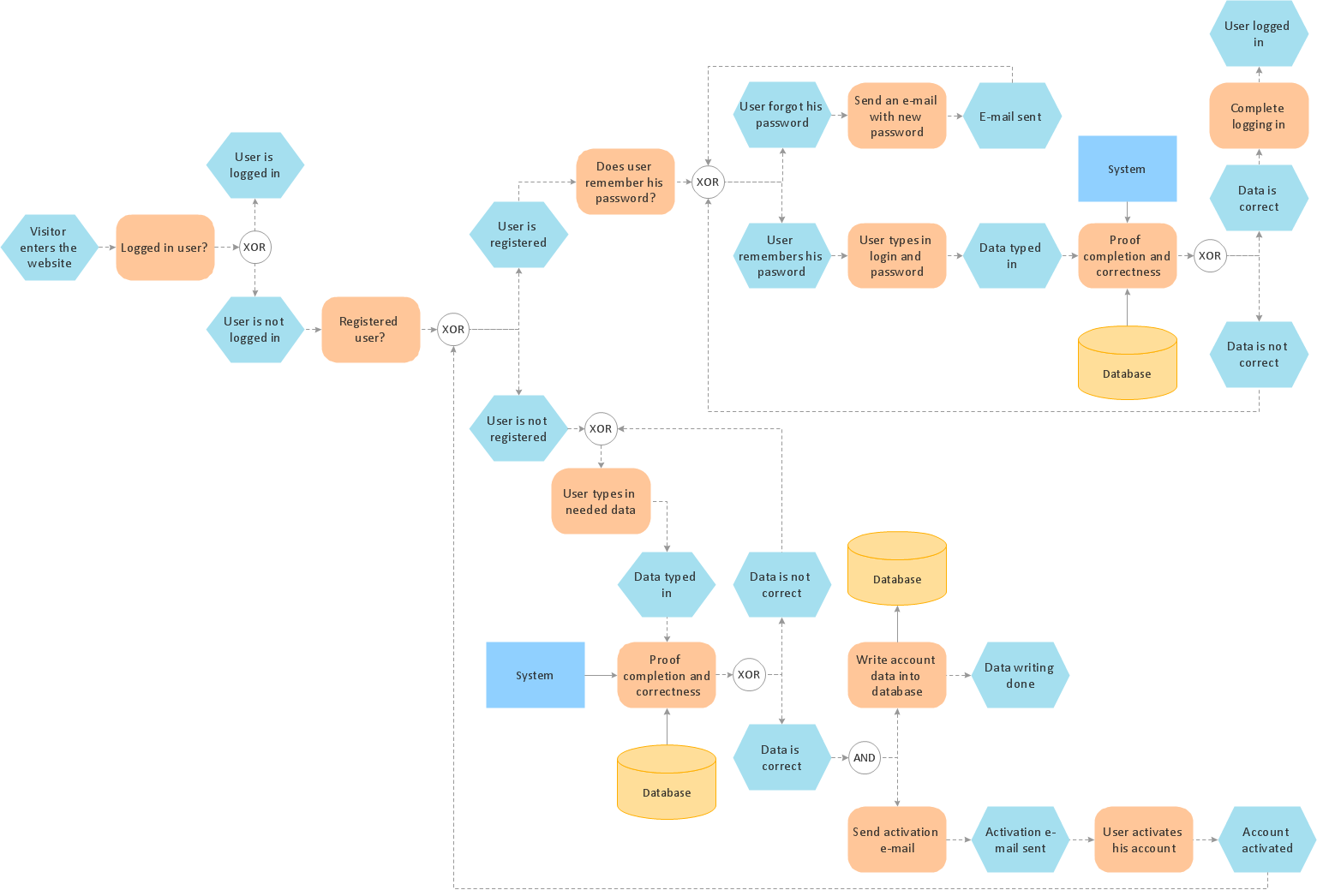
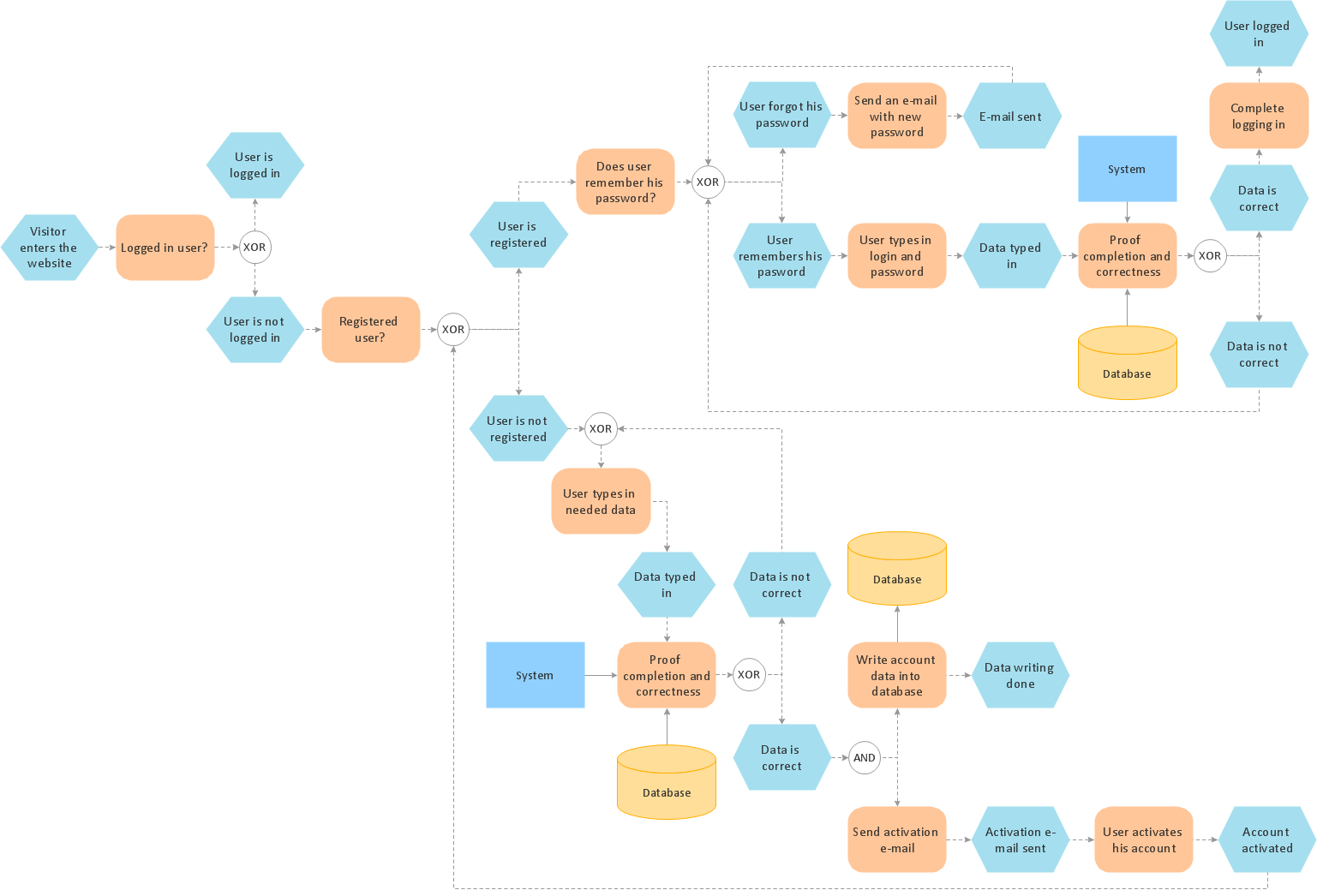
This event-driven process chain (EPC) flowchart sample depicts the login and registration processing.
"In computer security, a login or logon refers to the credentials required to obtain access to a computer system or other restricted area. Logging in or on and signing in or on is the process by which individual access to a computer system is controlled by identifying and authenticating the user through the credentials presented by the user.
Once a user has logged in, they can then log out or log off when access is no longer needed. To log out is to close off one's access to a computer system after having previously logged in." [Login. Wikipedia]
The event-driven process chain flowchart example "Login and registration processing" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Basic EPC solution from the Business Processes area of ConceptDraw Solution Park.
"In computer security, a login or logon refers to the credentials required to obtain access to a computer system or other restricted area. Logging in or on and signing in or on is the process by which individual access to a computer system is controlled by identifying and authenticating the user through the credentials presented by the user.
Once a user has logged in, they can then log out or log off when access is no longer needed. To log out is to close off one's access to a computer system after having previously logged in." [Login. Wikipedia]
The event-driven process chain flowchart example "Login and registration processing" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Basic EPC solution from the Business Processes area of ConceptDraw Solution Park.
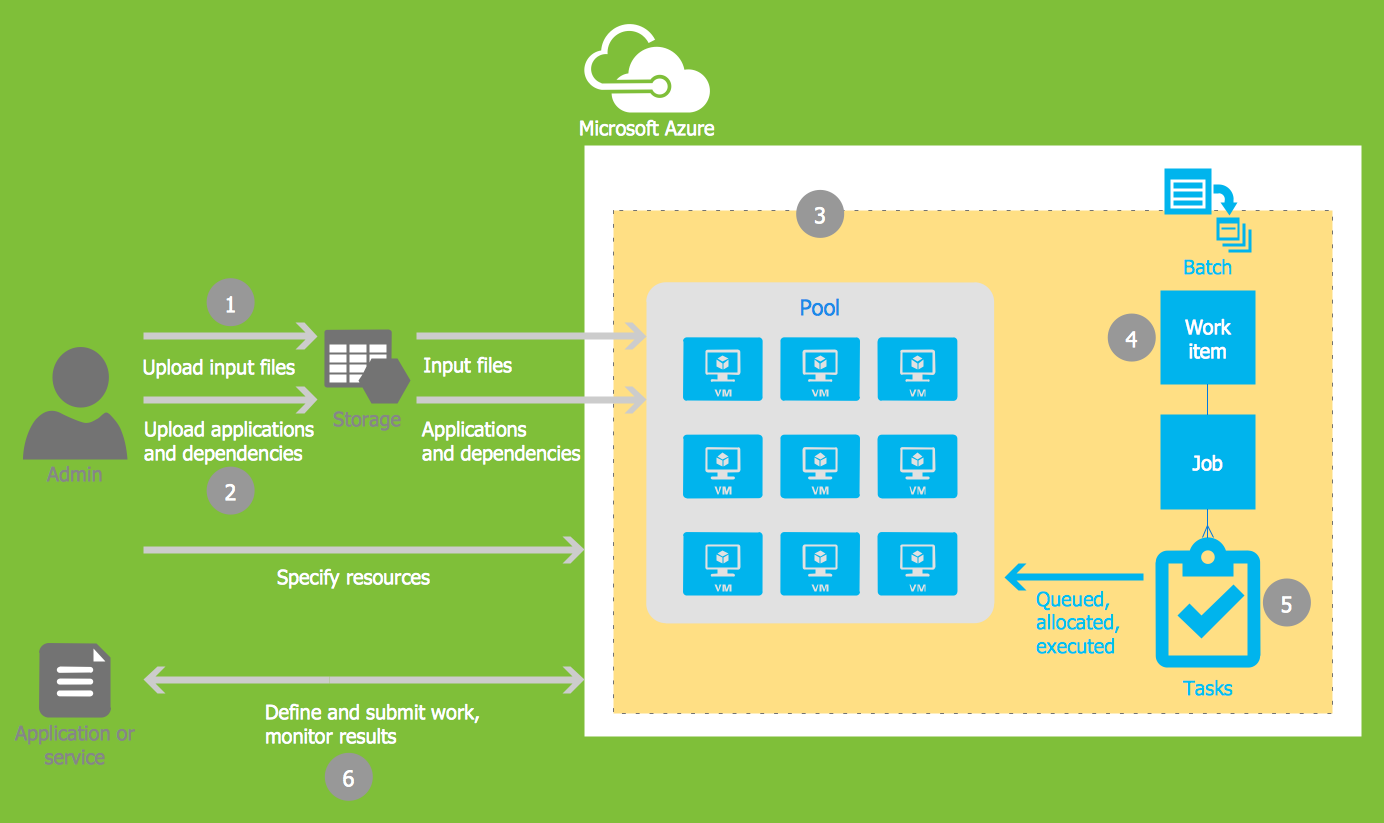
Microsoft Azure
Microsoft Azure is widely used cloud platform which was created by Microsoft and now is managed by Microsoft datacenters in 19 regions of the world, and has a wide set of benefits and features. ConceptDraw DIAGRAM diagramming and vector drawing software extended with Azure Architecture Solution from the Computer and Networks area of ConceptDraw Solution Park is the best for designing various pictorial infographics, illustrations and materials showing the possibilities and work of Microsoft Azure Cloud System and Azure services.How to Help Customers be More Productive
Presenting you with a drawing program which could really surprise you with their great functionality. Don't know how to start to draw Connector's improvement? Curious how should diagramming software work? Drawing programs involve a lot of things like designs in an illustrative way, creating an cherts, Tools to create high end graphics, create dashboards, using your data and many other technical aspects do it in a much professional and in a quick way.The vector stencils library "Cybersecurity" contains 24 cybersecurity icons.
Use it to design your computer and telecom illustrations and infographics with ConceptDraw PRO diagramming and vector drawing software.
The vector stencils library "Cybersecurity" is included in the Computers and Communications solution from the Illustration area of ConceptDraw Solution Park.
Use it to design your computer and telecom illustrations and infographics with ConceptDraw PRO diagramming and vector drawing software.
The vector stencils library "Cybersecurity" is included in the Computers and Communications solution from the Illustration area of ConceptDraw Solution Park.
Formalization and Verification of Event-driven Process chain
EPC or The Event - driven Process Chain diagrams that provide Enterprise Resource Planning improvement. ConceptDraw DIAGRAM - software that reduces the time needed to create a business process model.Flowchart
The Flowcharts are widespread in various fields and include the multitude of types. They are dedicated to representation the algorithms, processes, workflows of any complexity in a clear and intuitive format. The Flowcharts are commonly used in software development as a visual tool for illustration algorithms and logic of computer programs, in business for illustration business scenarios, in education, and so on. For drawing the Flowchart are used the special object blocks, among them rectangle or box used to represent an activity or step, rounded box or oval to depict Start / End, diamond to represent the decision point (involves the branching yes/no), circle used to represent the point of connection, parallelogram to represent the Input / Output, and some others. With ConceptDraw DIAGRAM including Flowcharts solution it is easy to create professional-looking Flowchart diagrams of any complexity and any degree of detailing. Succeed in drawing the Flowcharts using quick-start templates, predesigned samples and extensive libraries of ready-made flowchart symbols, blocks and icons.Process Modelling using Event-driven Process chain
Event-Driven Process Chain Diagrams for improvement throughout an organisation. ConceptDraw DIAGRAM - business process mapping software that reduces the time needed to create a business process model and its excellent business process improvement tools.EPC (Event-driven Process Chain) Flowcharts
The Event - driven Process Chain ( EPC ) allows managers visually present business process models for making decisions for business processes improvement. Event-Driven Process Сhain Diagrams for improvement throughout an organisation.- Cyber Security Png Lock
- Cloud clipart - Vector stencils library | Cloud round icons - Vector ...
- Data Flow Diagram For Login Module On Hotel Reservations
- Audio - Vector stencils library | Microphone 2d Png
- EPC diagrams - Vector stencils library | Event-driven process chain ...
- Login and registration processing | Login and registration ...
- Cybersecurity - Vector stencils library
- Login
- Cybersecurity - Vector stencils library | Cybersecurity - Vector ...