This computer security diagram example was designed on the base of the Wikimedia Commons file: Firewall.png.
[commons.wikimedia.org/ wiki/ File:Firewall.png]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
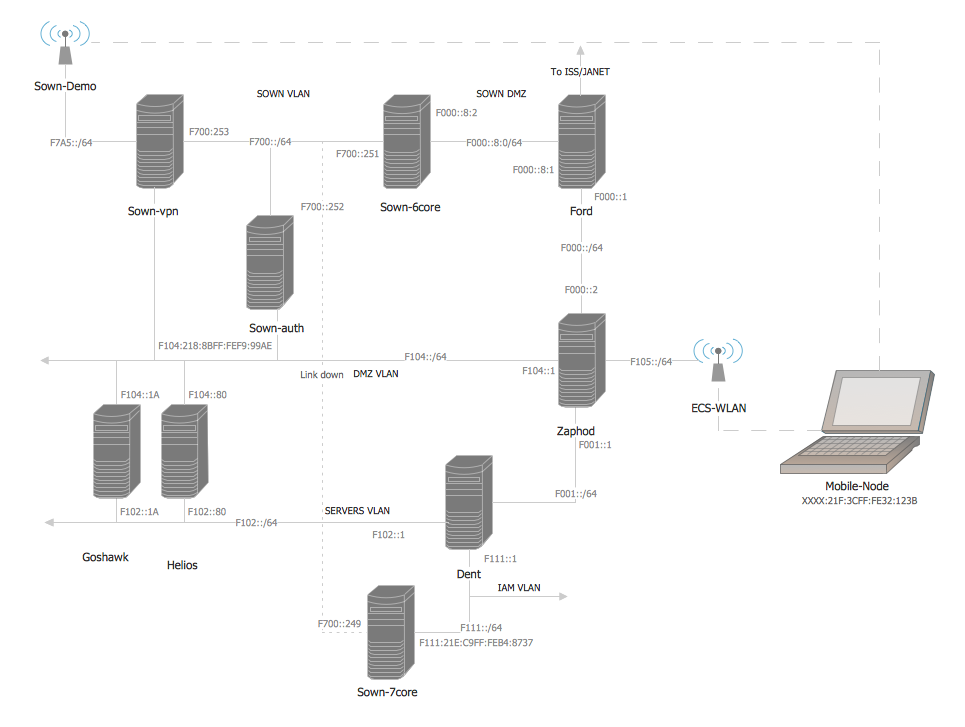
"In computing, a firewall is a network security system that monitors and controls the incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted, secure internal network and another outside network, such as the Internet, that is assumed to not be secure or trusted. Firewalls are often categorized as either network firewalls or host-based firewalls. Network firewalls are a software appliance running on general purpose hardware or hardware-based firewall computer appliances that filter traffic between two or more networks. Host-based firewalls provide a layer of software on one host that controls network traffic in and out of that single machine. Firewall appliances may also offer other functionality to the internal network they protect such as acting as a DHCP or VPN server for that network." [Firewall (computing). Wikipedia]
The cybersecurity diagram example "Firewall between LAN and WAN" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
[commons.wikimedia.org/ wiki/ File:Firewall.png]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"In computing, a firewall is a network security system that monitors and controls the incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted, secure internal network and another outside network, such as the Internet, that is assumed to not be secure or trusted. Firewalls are often categorized as either network firewalls or host-based firewalls. Network firewalls are a software appliance running on general purpose hardware or hardware-based firewall computer appliances that filter traffic between two or more networks. Host-based firewalls provide a layer of software on one host that controls network traffic in and out of that single machine. Firewall appliances may also offer other functionality to the internal network they protect such as acting as a DHCP or VPN server for that network." [Firewall (computing). Wikipedia]
The cybersecurity diagram example "Firewall between LAN and WAN" was created using the ConceprDraw PRO software extended with the Network Security Diagrams solution from the Computer and Neworks area of ConceptDraw Solution Park.
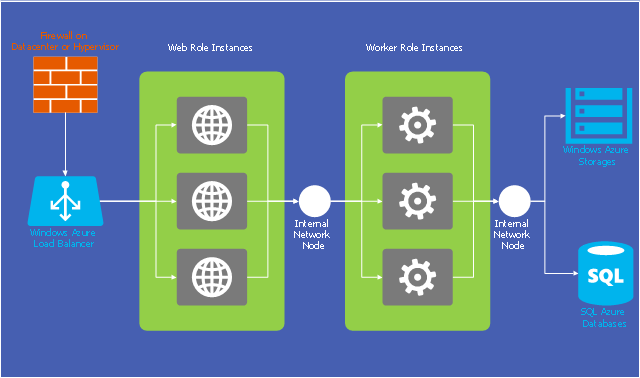
This example of cloud computing system architecture diagram was redesigned from the Wikimedia Commons file: Windows Azure Network and Computes Architecture.png. [commons.wikimedia.org/ wiki/ File:Windows_ Azure_ Network_ and_ Computes_ Architecture.png]
This file is licensed under the Creative Commons Attribution-Share Alike 2.0 license. [creativecommons.org/ licenses/ by-sa/ 2.0/ ]
"Microsoft Azure (formerly Windows Azure before 25 March 2014) is a cloud computing platform and infrastructure, created by Microsoft, for building, deploying and managing applications and services through a global network of Microsoft-managed datacenters. It provides both PaaS and IaaS services and supports many different programming languages, tools and frameworks, including both Microsoft-specific and third-party software and systems." [Microsoft Azure. Wikipedia]
The diagram example "Microsoft Azure network and computes architecture" was created using ConceptDraw PRO diagramming and vector drawing software extended with the Azure Architecture solution from the Computer and Networks area of ConceptDraw Solution Park.
This file is licensed under the Creative Commons Attribution-Share Alike 2.0 license. [creativecommons.org/ licenses/ by-sa/ 2.0/ ]
"Microsoft Azure (formerly Windows Azure before 25 March 2014) is a cloud computing platform and infrastructure, created by Microsoft, for building, deploying and managing applications and services through a global network of Microsoft-managed datacenters. It provides both PaaS and IaaS services and supports many different programming languages, tools and frameworks, including both Microsoft-specific and third-party software and systems." [Microsoft Azure. Wikipedia]
The diagram example "Microsoft Azure network and computes architecture" was created using ConceptDraw PRO diagramming and vector drawing software extended with the Azure Architecture solution from the Computer and Networks area of ConceptDraw Solution Park.
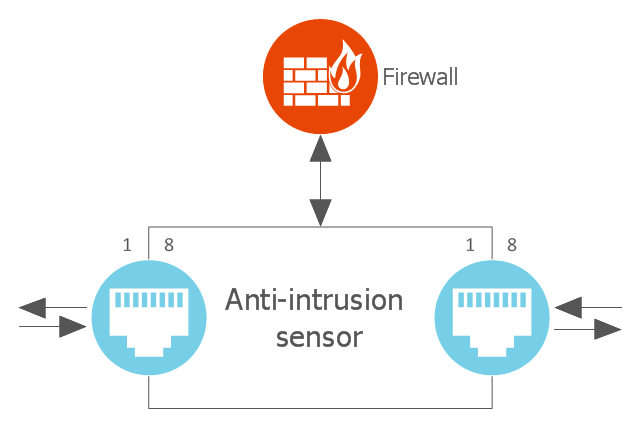
This cloud computing diagram example was drawn on the base of Wikimedia Commons file: ArchitectureptSonde.png.
"Figure representing the architecture of an anti-intrusion sensor for cloud computing." [commons.wikimedia.org/ wiki/ File:ArchitectureptSonde.png]
This file is made available under the Creative Commons CC0 1.0 Universal Public Domain Dedication. [creativecommons.org/ publicdomain/ zero/ 1.0/ deed.en]
"A wireless sensor network (WSN) (sometimes called a wireless sensor and actuator network (WSAN)) are spatially distributed autonomous sensors to monitor physical or environmental conditions, such as temperature, sound, pressure, etc. and to cooperatively pass their data through the network to a main location. The more modern networks are bi-directional, also enabling control of sensor activity. The development of wireless sensor networks was motivated by military applications such as battlefield surveillance; today such networks are used in many industrial and consumer applications, such as industrial process monitoring and control, machine health monitoring, and so on." [Wireless sensor network. Wikipedia]
The cloud computing diagram example "Anti-intrusion sensor architecture" was drawn using ConceptDraw PRO software extended with the Cloud Computing Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
"Figure representing the architecture of an anti-intrusion sensor for cloud computing." [commons.wikimedia.org/ wiki/ File:ArchitectureptSonde.png]
This file is made available under the Creative Commons CC0 1.0 Universal Public Domain Dedication. [creativecommons.org/ publicdomain/ zero/ 1.0/ deed.en]
"A wireless sensor network (WSN) (sometimes called a wireless sensor and actuator network (WSAN)) are spatially distributed autonomous sensors to monitor physical or environmental conditions, such as temperature, sound, pressure, etc. and to cooperatively pass their data through the network to a main location. The more modern networks are bi-directional, also enabling control of sensor activity. The development of wireless sensor networks was motivated by military applications such as battlefield surveillance; today such networks are used in many industrial and consumer applications, such as industrial process monitoring and control, machine health monitoring, and so on." [Wireless sensor network. Wikipedia]
The cloud computing diagram example "Anti-intrusion sensor architecture" was drawn using ConceptDraw PRO software extended with the Cloud Computing Diagrams solution from the Computer and Networks area of ConceptDraw Solution Park.
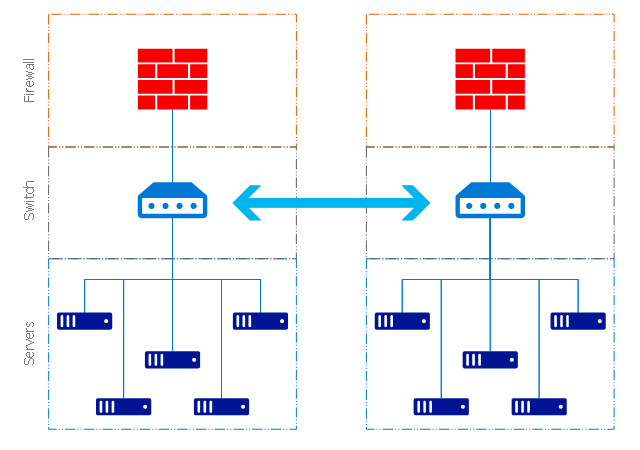
This example of cloud computing system architecture diagram was redesigned from the Wikimedia Commons file: ArchitectureCloudLinksSameSite.png. [commons.wikimedia.org/ wiki/ File:ArchitectureCloudLinksSameSite.png]
"An example showing a grid computing system connecting many personal computers over the Internet using inter-process network communication ...
In computer science, inter-process communication (IPC) is the activity of sharing data across multiple and commonly specialized processes using communication protocols. Typically, applications using IPC are categorized as clients and servers, where the client requests data and the server responds to client requests." [en.wikipedia.org/ wiki/ Inter-process_ communication]
"Grid computing is the collection of computer resources from multiple locations to reach a common goal. The grid can be thought of as a distributed system with non-interactive workloads that involve a large number of files. Grid computing is distinguished from conventional high performance computing systems such as cluster computing in that grid computers have each node set to perform a different task/ application. Grid computers also tend to be more heterogeneous and geographically dispersed (thus not physically coupled) than cluster computers." [Grid computing. Wikipedia]
The diagram example "Grid computing system architecture" was created using ConceptDraw PRO diagramming and vector drawing software extended with the Azure Architecture solution from the Computer and Networks area of ConceptDraw Solution Park.
"An example showing a grid computing system connecting many personal computers over the Internet using inter-process network communication ...
In computer science, inter-process communication (IPC) is the activity of sharing data across multiple and commonly specialized processes using communication protocols. Typically, applications using IPC are categorized as clients and servers, where the client requests data and the server responds to client requests." [en.wikipedia.org/ wiki/ Inter-process_ communication]
"Grid computing is the collection of computer resources from multiple locations to reach a common goal. The grid can be thought of as a distributed system with non-interactive workloads that involve a large number of files. Grid computing is distinguished from conventional high performance computing systems such as cluster computing in that grid computers have each node set to perform a different task/ application. Grid computers also tend to be more heterogeneous and geographically dispersed (thus not physically coupled) than cluster computers." [Grid computing. Wikipedia]
The diagram example "Grid computing system architecture" was created using ConceptDraw PRO diagramming and vector drawing software extended with the Azure Architecture solution from the Computer and Networks area of ConceptDraw Solution Park.
Network Security
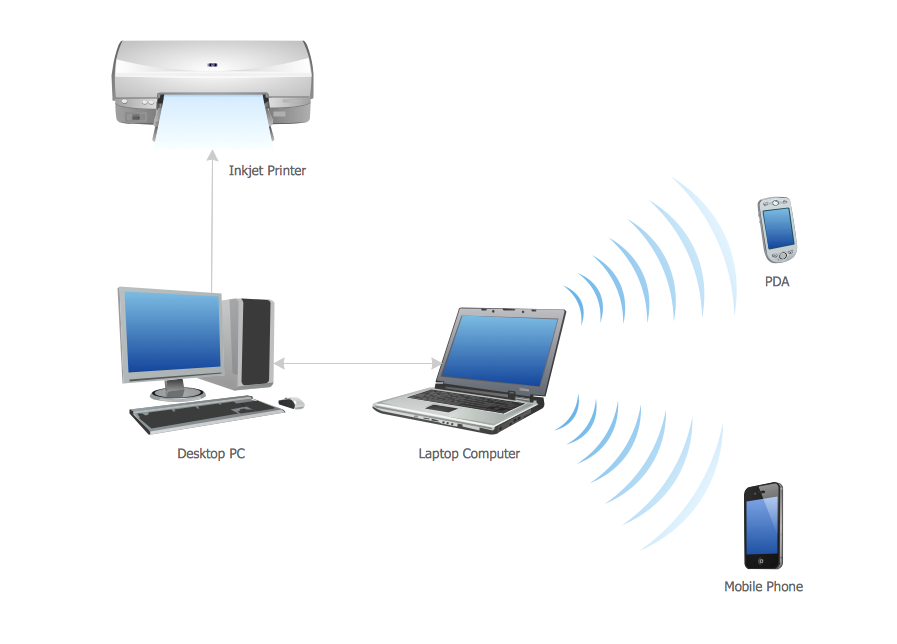
The Internet is a giant computer network which connects computers all over the world. It is integral part of human society and business. But the serious question for network engineers, designers, lawmakers and enforcers is the need for protect the Internet networks from the Internet crimes, hacking and attacks. There are quite a number of hardware, software and physical methods of protection against them. The samples you see on this page were created in ConceptDraw DIAGRAM using the tools of Network Security Diagrams Solution for ConceptDraw DIAGRAM software. They show protection networks with Firewalls and other network security devices.Cisco Network Design. Cisco icons, shapes, stencils, symbols and design elements
Cisco is the largest company, which specializes in the field of high technologies, develops and sells network equipment mainly for the large organizations and telecommunication companies. Cisco produces wide variety of devices and equipment, such as routers, switches, gateways, servers, network security devices (firewalls, VPN, IDs, etc.), ATM switches, cable modems and DSL equipment, access points Wi-Fi, products for IP telephony, etc. The first commercially successful multi-protocol router, which enabled for previously incompatible computers to communicate between themselves, is also developed by Cisco company. Cisco is a generally accepted standard, which uses globally recognized Cisco icons for all produced Cisco equipment. ConceptDraw DIAGRAM software extended with Cisco Network Diagrams solution from Computer and Network area contains a lot of predesigned Cisco network design elements for professional drawing Cisco network diagrams, visualization computer network topologies, equipment connections and arrangement.Network Security Devices
How to describe the necessity of using network security devices and visually illustrate this information? Now, it's very easy thanks to the ConceptDraw DIAGRAM diagramming and vector drawing software extended with Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park.Personal area (PAN) networks. Computer and Network Examples
Personal area network (PAN) is a network organized on a limited area and used for data transmission between various personal devices, such as computers, tablets, laptops, telephones, different digital and mobile devices, etc. and also for connecting to higher level network and Internet. PAN is used to manage the interconnections of IT devices which surround a single user and generally contains such appliances, as cordless mice, keyboard, phone, and Bluetooth handsets. PANs can be wired with computer buses, or wirelessly connected to the Internet using such network technologies as Bluetooth, Z-Wave, ZigBee, IrDa, UWB, Body Area Network. PANs have a lot of pros and cons, they are expedient, lucrative and handy, but sometimes have bad connection with other networks on the same radio bands, Bluetooth has distance limits and slow data transfer speed, but is comparatively safe. ConceptDraw DIAGRAM diagramming software supplied with numerous solutions of Computer and Networks Area included to ConceptDraw Solution Park perfectly suits for designing the Personal Area Networks.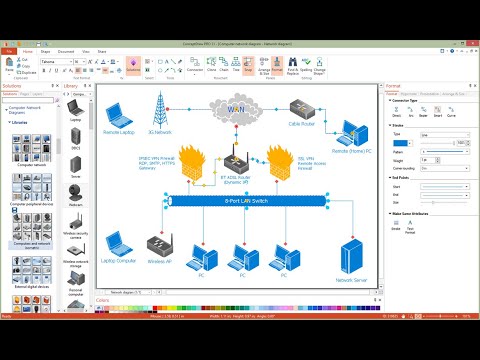
Cisco Products Additional. Cisco icons, shapes, stencils and symbols
The ConceptDraw vector stencils library Cisco Products Additional contains equipment symbols for drawing the computer network diagrams.The vector stencils library "Computers and network isometric" contains 56 3D clipart images of computer and network devices and equipment for drawing network diagrams.
The clip art example "Computers and network isometric - Vector stencils library" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Computer and Networks solution from the Computer and Networks area of ConceptDraw Solution Park.
The clip art example "Computers and network isometric - Vector stencils library" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Computer and Networks solution from the Computer and Networks area of ConceptDraw Solution Park.
- Firewall between LAN and WAN | Cisco Network Diagrams ...
- Firewall between LAN and WAN | Access and security - Vector ...
- Firewall between LAN and WAN | Network Security Diagrams ...
- Hydraulic circuits | Firewall between LAN and WAN | Loyalty - Arrow ...
- Design elements - Workflow connectors | Firewall between LAN and ...
- Firewall between LAN and WAN | Network Security | AD LDS as a ...
- Network Security | Network Security Devices | Firewall between LAN ...
- Firewall between LAN and WAN | Network Security | Network ...
- Physical LAN and WAN diagram - Template | Network Diagram ...
- Firewall between LAN and WAN | Computer and Internet use at ...