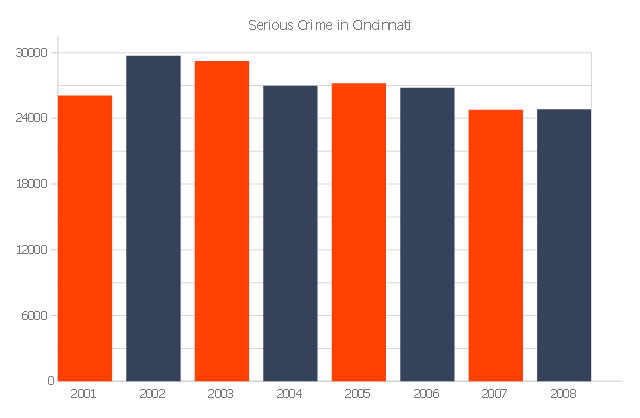
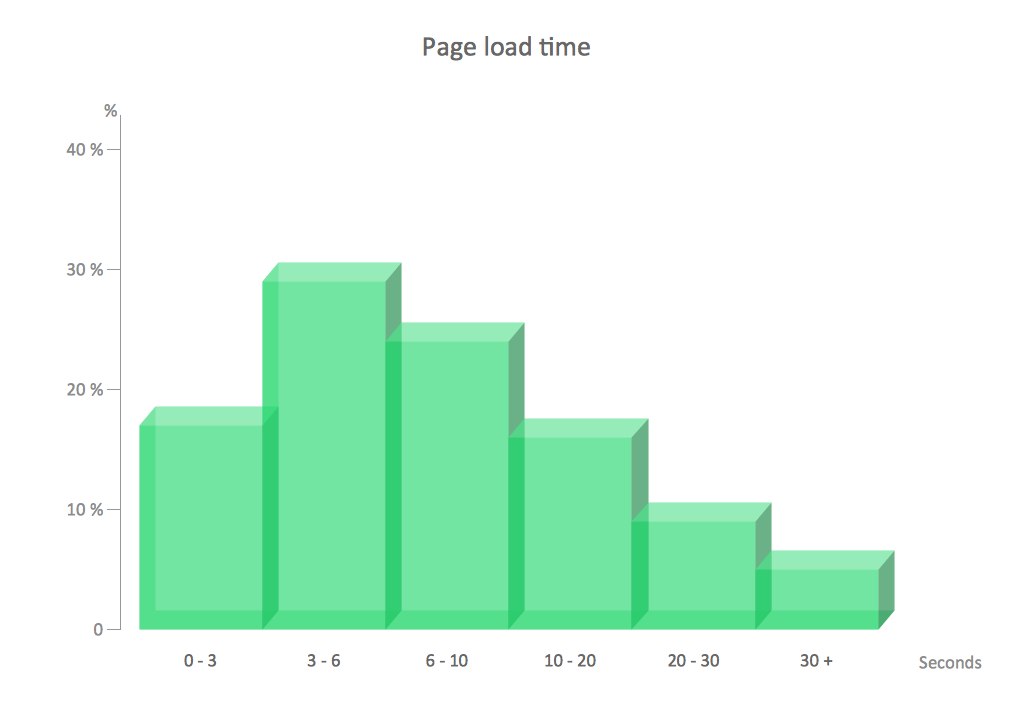
The vertical bar graph sample shows the serious crime number in Cincinnati from 2001 to 2008. It was designed on the base of the Commons Wikimedia file: Cincinnati-Part-1-Crimes.jpg.
[commons.wikimedia.org/ wiki/ File:Cincinnati-Part-1-Crimes.jpg]
"Before the riot of 2001, Cincinnati's overall crime rate was dropping dramatically and had reached its lowest point since 1992. After the riot violent crime increased. Reflecting national trends, crime rates in Cincinnati have dropped in all categories from 2006 to 2010." [Crime in Cincinnati. Wikipedia]
The column chart example "Serious crime in Cincinnati" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Bar Graphs solution from the Graphs and Charts area of ConceptDraw Solution Park.
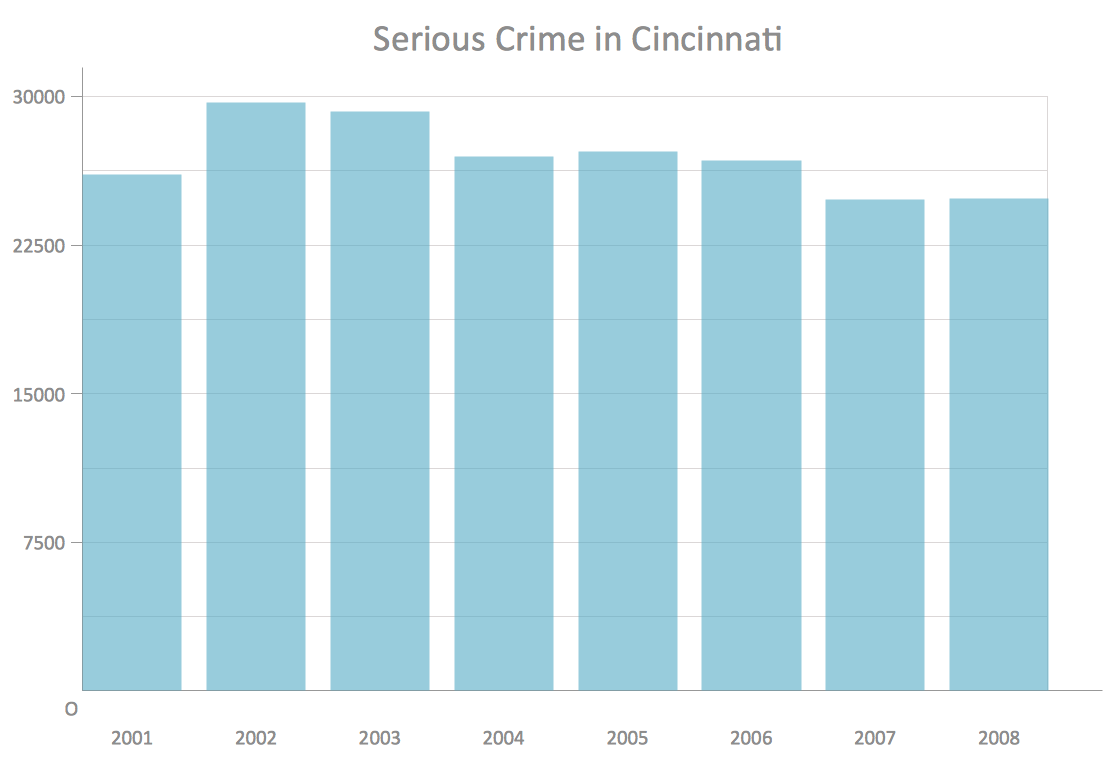
[commons.wikimedia.org/ wiki/ File:Cincinnati-Part-1-Crimes.jpg]
"Before the riot of 2001, Cincinnati's overall crime rate was dropping dramatically and had reached its lowest point since 1992. After the riot violent crime increased. Reflecting national trends, crime rates in Cincinnati have dropped in all categories from 2006 to 2010." [Crime in Cincinnati. Wikipedia]
The column chart example "Serious crime in Cincinnati" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Bar Graphs solution from the Graphs and Charts area of ConceptDraw Solution Park.
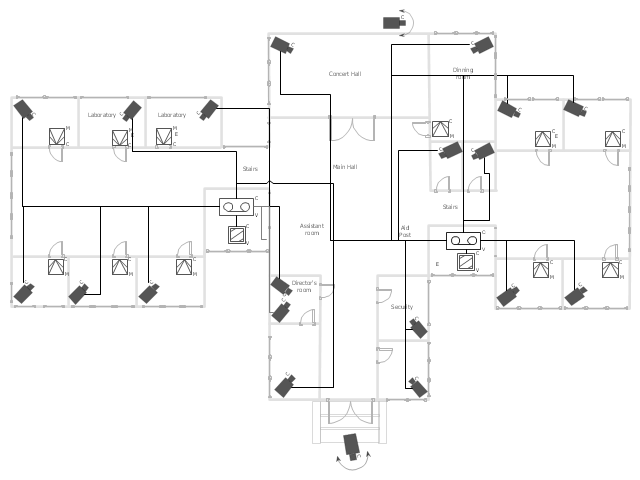
This example was drawn on the base of the floor plan from the website of the School of Criminal Justice at Rutgers University. [crimeprevention.rutgers.edu/ crime/ emp_ theft/ warehouses/ quiz2.htm]
"Preventing Theft from Warehouses.
The biggest threat to warehouses is collusion between two dishonest people - one inside the warehouse who is employed by you, and another person outside. Your warehouse is vulnerable in different ways at each step of the handling of merchandise. Below, we've broken this process down into three major steps: receiving, storage, and shipping." [crimeprevention.rutgers.edu/ crime/ emp_ theft/ warehouses/ warehouses.htm]
"Storage.
The trucks have been unloaded and everything put away on the shelves in the warehouse. Now your merchandise is even more vulnerable to thieves than before.
There are two main elements of a good security plan:
1) Keep people out of areas where they don't belong...
2) Keep track of what goods are supposed to be in your warehouse" [crimeprevention.rutgers.edu/ crime/ emp_ theft/ warehouses/ storage/ storage.htm]
The floor plan example "Warehouse security quiz" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Plant Layout Plans solution from the Building Plans area of ConceptDraw Solution Park.
"Preventing Theft from Warehouses.
The biggest threat to warehouses is collusion between two dishonest people - one inside the warehouse who is employed by you, and another person outside. Your warehouse is vulnerable in different ways at each step of the handling of merchandise. Below, we've broken this process down into three major steps: receiving, storage, and shipping." [crimeprevention.rutgers.edu/ crime/ emp_ theft/ warehouses/ warehouses.htm]
"Storage.
The trucks have been unloaded and everything put away on the shelves in the warehouse. Now your merchandise is even more vulnerable to thieves than before.
There are two main elements of a good security plan:
1) Keep people out of areas where they don't belong...
2) Keep track of what goods are supposed to be in your warehouse" [crimeprevention.rutgers.edu/ crime/ emp_ theft/ warehouses/ storage/ storage.htm]
The floor plan example "Warehouse security quiz" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Plant Layout Plans solution from the Building Plans area of ConceptDraw Solution Park.
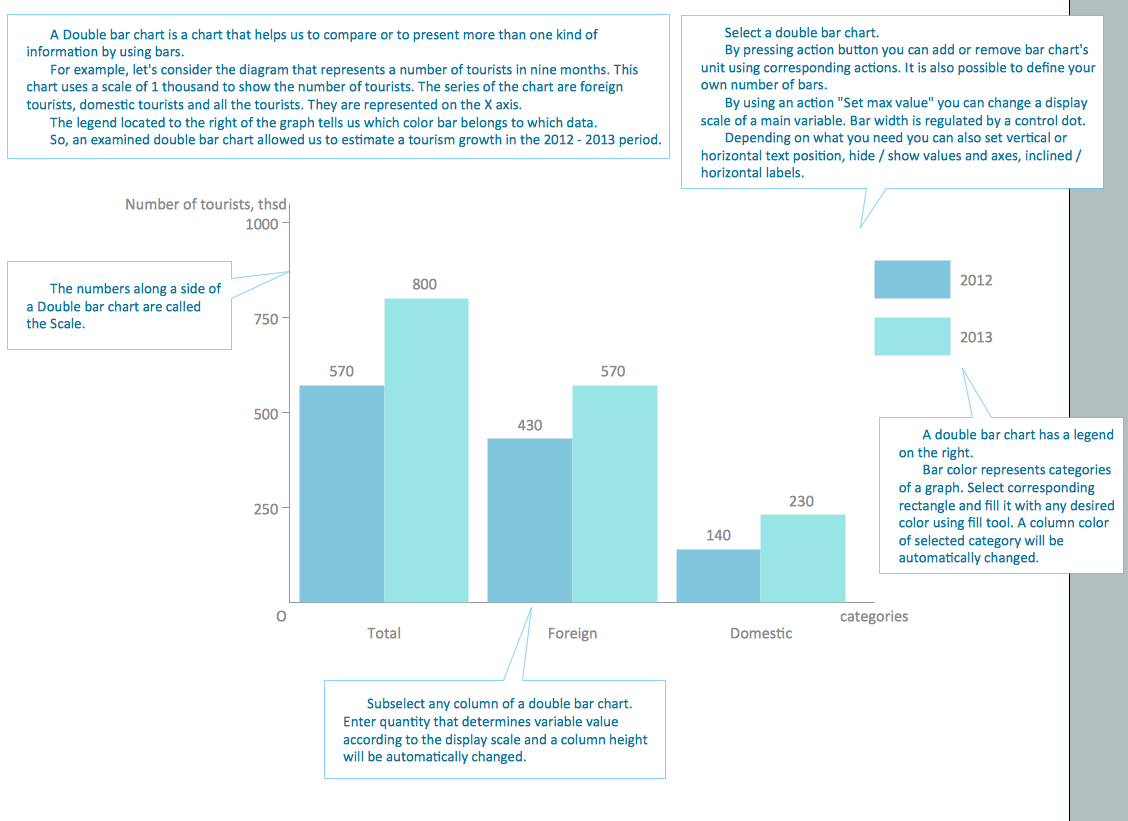
How to Create a Column Chart
The question how to create a column chart have a simple answer. Use ConceptDraw tips to find out how to create a column chart depicts your data the best way.Column Chart Examples
Column chart examples from ConceptDraw collection can help you find the best visual depiction for you data. You can easily modify column chart examples according to data you want to visualize."Closed-circuit television (CCTV) is the use of video cameras to transmit a signal to a specific place, on a limited set of monitors. It differs from broadcast television in that the signal is not openly transmitted, though it may employ point to point (P2P), point to multipoint, or mesh wireless links. Though almost all video cameras fit this definition, the term is most often applied to those used for surveillance in areas that may need monitoring such as banks, casinos, airports, military installations, and convenience stores. Videotelephony is seldom called "CCTV" but the use of video in distance education, where it is an important tool, is often so called.
In industrial plants, CCTV equipment may be used to observe parts of a process from a central control room, for example when the environment is not suitable for humans. CCTV systems may operate continuously or only as required to monitor a particular event. A more advanced form of CCTV, utilizing digital video recorders (DVRs), provides recording for possibly many years, with a variety of quality and performance options and extra features (such as motion detection and email alerts). More recently, decentralized IP cameras, some equipped with megapixel sensors, support recording directly to network-attached storage devices, or internal flash for completely stand-alone operation. Surveillance of the public using CCTV is particularly common in many areas around the world. In recent years, the use of body worn video cameras has been introduced as a new form of surveillance. ... In the United States, closed-circuit television is used for school security to monitor visitors, track unacceptable student behavior and maintain a record of evidence in the event of a crime. There are some restrictions on installation, cameras may not be used in an area where there is a "reasonable expectation of privacy". Examples of these are bathrooms, gym locker areas and private offices (unless consent by the office owner is given). Сameras are generally acceptable in hallways, parking lots, front offices where students, employees, and parents come and go, gymnasiums, cafeterias, supply rooms and classrooms. The use of cameras in classrooms is often debated by teachers who want cameras for protection and teachers who do not." [Closed-circuit television. Wikipedia]
The floor plan example "Video surveillance scheme" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Security and Access Plans solution from the Building Plans area of ConceptDraw Solution Park.
In industrial plants, CCTV equipment may be used to observe parts of a process from a central control room, for example when the environment is not suitable for humans. CCTV systems may operate continuously or only as required to monitor a particular event. A more advanced form of CCTV, utilizing digital video recorders (DVRs), provides recording for possibly many years, with a variety of quality and performance options and extra features (such as motion detection and email alerts). More recently, decentralized IP cameras, some equipped with megapixel sensors, support recording directly to network-attached storage devices, or internal flash for completely stand-alone operation. Surveillance of the public using CCTV is particularly common in many areas around the world. In recent years, the use of body worn video cameras has been introduced as a new form of surveillance. ... In the United States, closed-circuit television is used for school security to monitor visitors, track unacceptable student behavior and maintain a record of evidence in the event of a crime. There are some restrictions on installation, cameras may not be used in an area where there is a "reasonable expectation of privacy". Examples of these are bathrooms, gym locker areas and private offices (unless consent by the office owner is given). Сameras are generally acceptable in hallways, parking lots, front offices where students, employees, and parents come and go, gymnasiums, cafeterias, supply rooms and classrooms. The use of cameras in classrooms is often debated by teachers who want cameras for protection and teachers who do not." [Closed-circuit television. Wikipedia]
The floor plan example "Video surveillance scheme" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Security and Access Plans solution from the Building Plans area of ConceptDraw Solution Park.
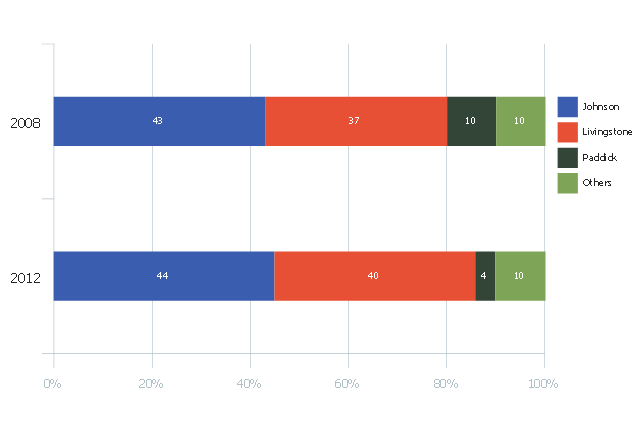
This divided bar diagram sample shows London election results in 2008 and 2012. It was drawn using data from the infographics "London Elections Results by Numbers" on the london.gov.uk website.
[data.london.gov.uk/ datastore/ package/ london-elections-results-2012-wards-boroughs-constituency]
"There are six types of elections in the United Kingdom: United Kingdom general elections, elections to devolved parliaments and assemblies, elections to the European Parliament, local elections, mayoral elections and Police and Crime Commissioner elections. Elections are held on Election Day, which is conventionally a Thursday. General elections do not have fixed dates, but must be called within five years of the opening of parliament following the last election. Other elections are held on fixed dates, though in the case of the devolved assemblies and parliaments early elections can occur in certain situations. Currently, six electoral systems are used: the single member plurality system (First Past the Post), the multi member plurality system, party list PR, the single transferable vote, the Additional Member System and the Supplementary Vote.
Elections are administered locally: in each lower-tier local authority, the actual polling procedure is run by the Returning Officer and the compiling and maintenance of the electoral roll by the Electoral Registration Officer (except in Northern Ireland, where the Electoral Office for Northern Ireland assumes both responsibilities). The Electoral Commission only sets standards for and issues guidelines to Returning Officers and Electoral Registration Officers, but is responsible for nationwide electoral administration (such as the registration of political parties and directing the administration of national referendums)." [Elections in the United Kingdom. Wikipedia]
The chart example "London election results" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Divided Bar Diagrams solution from the Graphs and Charts area of ConceptDraw Solution Park.
[data.london.gov.uk/ datastore/ package/ london-elections-results-2012-wards-boroughs-constituency]
"There are six types of elections in the United Kingdom: United Kingdom general elections, elections to devolved parliaments and assemblies, elections to the European Parliament, local elections, mayoral elections and Police and Crime Commissioner elections. Elections are held on Election Day, which is conventionally a Thursday. General elections do not have fixed dates, but must be called within five years of the opening of parliament following the last election. Other elections are held on fixed dates, though in the case of the devolved assemblies and parliaments early elections can occur in certain situations. Currently, six electoral systems are used: the single member plurality system (First Past the Post), the multi member plurality system, party list PR, the single transferable vote, the Additional Member System and the Supplementary Vote.
Elections are administered locally: in each lower-tier local authority, the actual polling procedure is run by the Returning Officer and the compiling and maintenance of the electoral roll by the Electoral Registration Officer (except in Northern Ireland, where the Electoral Office for Northern Ireland assumes both responsibilities). The Electoral Commission only sets standards for and issues guidelines to Returning Officers and Electoral Registration Officers, but is responsible for nationwide electoral administration (such as the registration of political parties and directing the administration of national referendums)." [Elections in the United Kingdom. Wikipedia]
The chart example "London election results" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Divided Bar Diagrams solution from the Graphs and Charts area of ConceptDraw Solution Park.
Column Chart Template
Column chart templates from ConceptDraw collection can help you find the best visual depiction for you data. You can easily modify column chart templates according to data you want to visualize.Chart Templates
Easy charting software comes with beautiful chart templates and examples. This makes it easy to create professional charts without prior experience.Chart Examples
Easy charting software comes with beautiful chart templates and examples. This makes it easy to create professional charts without prior experience.Network Security
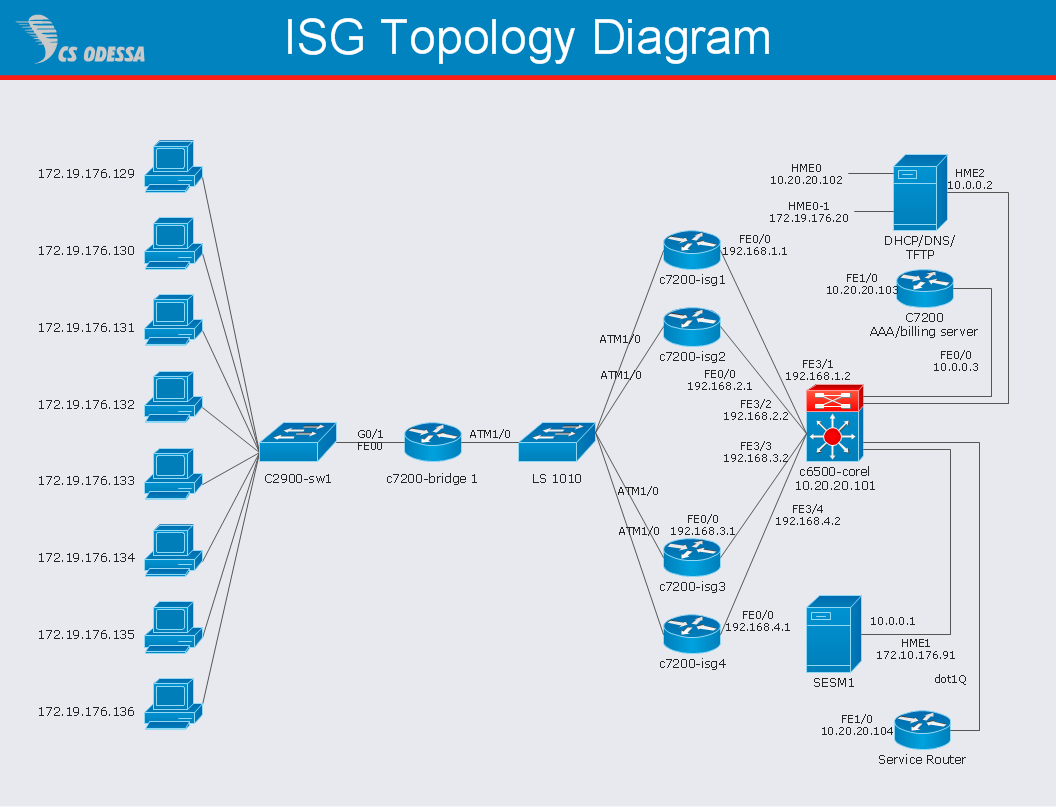
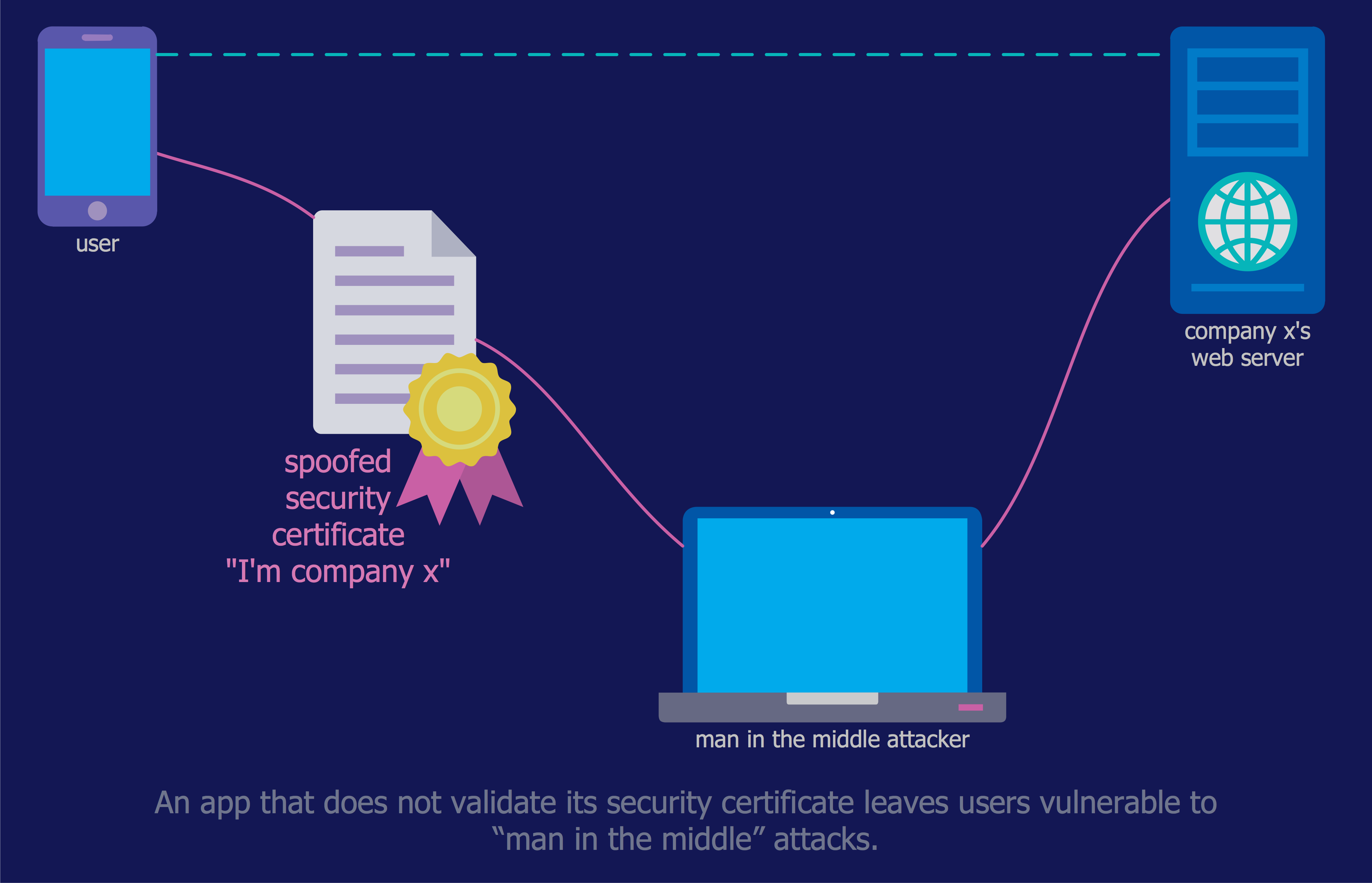
The Internet is a giant computer network which connects computers all over the world. It is integral part of human society and business. But the serious question for network engineers, designers, lawmakers and enforcers is the need for protect the Internet networks from the Internet crimes, hacking and attacks. There are quite a number of hardware, software and physical methods of protection against them. The samples you see on this page were created in ConceptDraw PRO using the tools of Network Security Diagrams Solution for ConceptDraw PRO software. They show protection networks with Firewalls and other network security devices.
 Bar Graphs
Bar Graphs
The Bar Graphs solution enhances ConceptDraw PRO v10 functionality with templates, numerous professional-looking samples, and a library of vector stencils for drawing different types of Bar Graphs, such as Simple Bar Graph, Double Bar Graph, Divided Bar Graph, Horizontal Bar Graph, Vertical Bar Graph, and Column Bar Chart.
Network Diagram Software ISG Network Diagram
Drawing ISG Network Diagram using ConceptDraw PRO stencils
IT Security Solutions
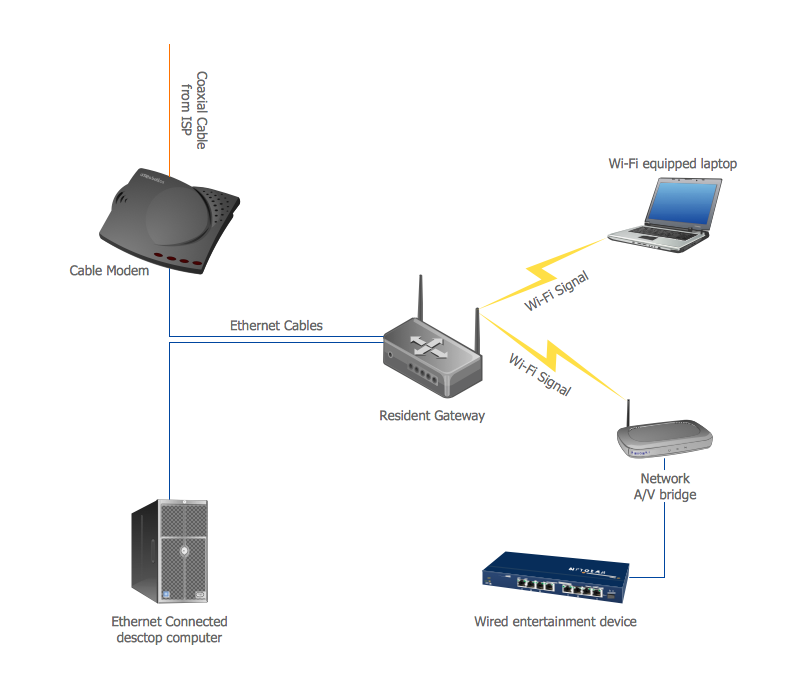
Dynamic of development computer and network technologies increases the need in modern cyber security strategies and IT security solutions to support security of your data, to ensure data privacy, and to protect your operations from the cyber threats. Thanks to the Network Security Diagrams Solution from the Computer and Networks Area of ConceptDraw Solution Park, the ConceptDraw PRO diagramming and vector drawing software is one of the unique IT security solutions for professional designing Network Security Diagrams.Home area networks (HAN). Computer and Network Examples
A Home Area Networks (HAN) is a type of local area network that is used in an individual home. The home computers can be connected together by twisted pair or by a wireless network. HAN facilitates the communication and interoperability among digital devices at the home, allows to easier access to the entertainments and increase the productivity, organize the home security. This example was created in ConceptDraw PRO using the Computer and Networks Area of ConceptDraw Solution Park and shows the home network diagram.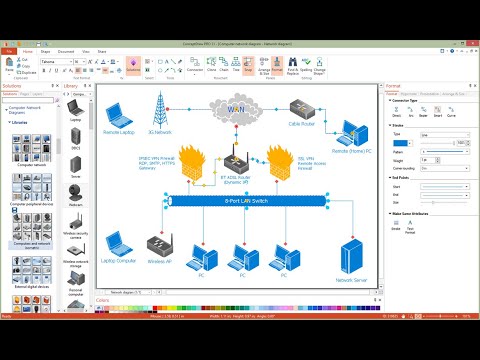
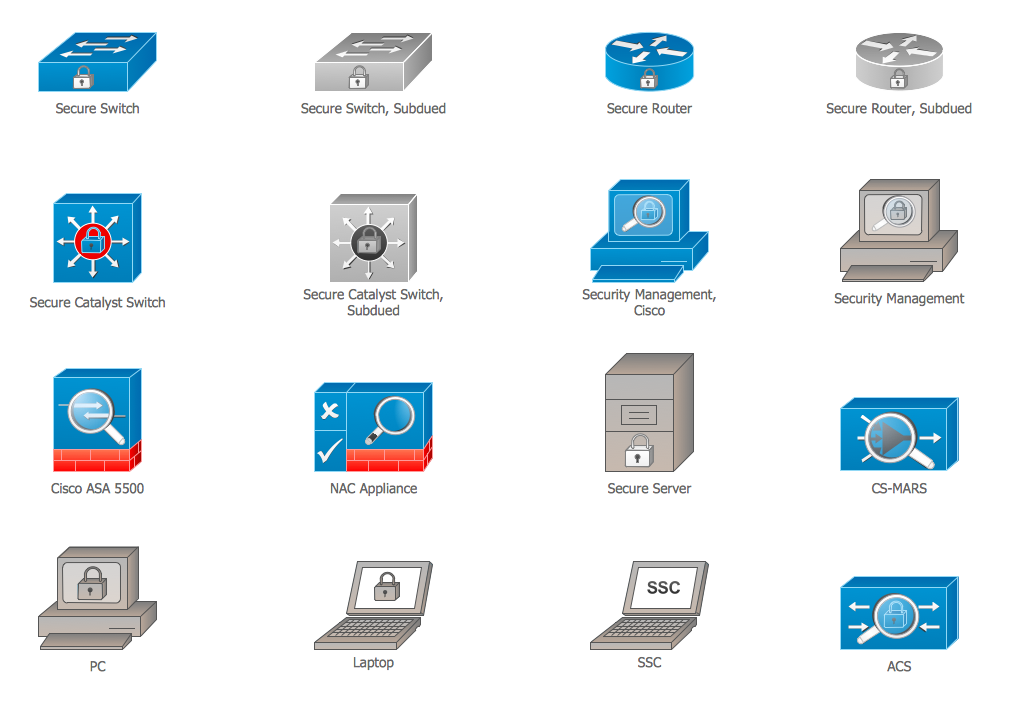
Cisco Security. Cisco icons, shapes, stencils and symbols
The ConceptDraw vector stencils library "Cisco Security" contains 16 symbols of security devices and equipment for drawing the computer network diagrams using the ConceptDraw PRO diagramming and vector drawing software.- Serious crime in Cincinnati | How to Create a Column Chart ...
- Serious crime in Cincinnati | Bar Graphs | Chart Examples | Crime ...
- Problem Solving Crime Flow Diagram
- Serious crime in Cincinnati | Bar Graphs | Serious crime in ...
- Serious crime in Cincinnati | Chart Maker for Presentations | Column ...
- Crime Problem Solving Diagram
- Give Me Flow Diagram Of The Processes To Solve Crime
- Draw A Flow Diagram Of The Process To Slove Crime
- Bar Graphs | Chart Examples | Column Chart Examples | Crime In ...
- Flow Diagram Of Processes In Solving Crime
- Flow Diagram Of The Processes To Solve Crime
- Diagram For How To Solve Crime
- A Diagram Of Processes Of Sokve Crime
- Draw A Flow Diagram Of Processes To Solve Crime
- Diagrams And Graphs Of Crime
- Spider Diagram Crime Solving
- Bar Graphs | Column Chart Template | Barchart Of Computer Crime
- Bar Graph | Serious crime in Cincinnati | Bar Diagrams for Problem ...
- Flow Chart Of Solving Crime