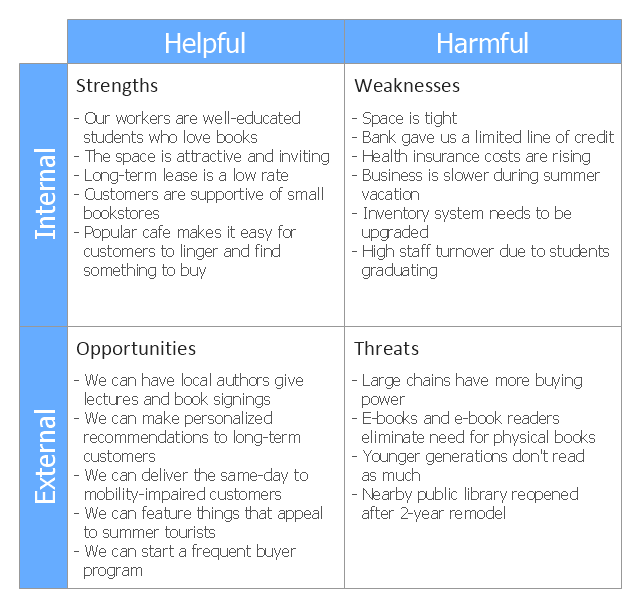
This SWOT matrix diagram example was created on the base of article "An Easy Way To Jumpstart Your Strategic Plan: SWOT" by Leslie Wolf from the website of the California Digital Library, the University of California. "Strategic planning doesn’t have to be a daunting and lengthy process. The goal is really a simple one: to help you understand your world and build a road map to guide your efforts. ...
This analysis tool can help you focus your attention on the specific success factors that are right for your team.
The tool is called a SWOT analysis. SWOT stands for Strengths and Weaknesses, Opportunities and Threats. Here’s what it means:
(1) Strengths are those positive internal attributes that strengthen your business or team. You can develop plans to capitalize on those strengths.
(2) Weaknesses are those negative internal attributes that are working against your success. You can shore up those weaknesses so they don’t stop your success.
(3) Opportunities are those external conditions that can have a positive effect on your goals. These opportunities can point you in the right direction.
(4) Threats are those external conditions that can have a negative effect on your goals. These threats will affect you less if you can identify and minimize them. ...
We thought it would be helpful to show you a sample SWOT analysis for a business you can easily visualize: a small independent bookstore in a university town. The store owner brought the team together to think about how the bookstore could survive during the continuing financial downturn. After an hour of brainstorming, this is the SWOT analysis they developed." [cdlib.org/ cdlinfo/ 2010/ 09/ 29/ an-easy-way-to-jumpstart-your-strategic-plan-swot/ ]
The matrix diagram example "SWOT analysis for a small independent bookstore" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the SWOT Analysis solution from the Management area of ConceptDraw Solution Park.
This analysis tool can help you focus your attention on the specific success factors that are right for your team.
The tool is called a SWOT analysis. SWOT stands for Strengths and Weaknesses, Opportunities and Threats. Here’s what it means:
(1) Strengths are those positive internal attributes that strengthen your business or team. You can develop plans to capitalize on those strengths.
(2) Weaknesses are those negative internal attributes that are working against your success. You can shore up those weaknesses so they don’t stop your success.
(3) Opportunities are those external conditions that can have a positive effect on your goals. These opportunities can point you in the right direction.
(4) Threats are those external conditions that can have a negative effect on your goals. These threats will affect you less if you can identify and minimize them. ...
We thought it would be helpful to show you a sample SWOT analysis for a business you can easily visualize: a small independent bookstore in a university town. The store owner brought the team together to think about how the bookstore could survive during the continuing financial downturn. After an hour of brainstorming, this is the SWOT analysis they developed." [cdlib.org/ cdlinfo/ 2010/ 09/ 29/ an-easy-way-to-jumpstart-your-strategic-plan-swot/ ]
The matrix diagram example "SWOT analysis for a small independent bookstore" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the SWOT Analysis solution from the Management area of ConceptDraw Solution Park.
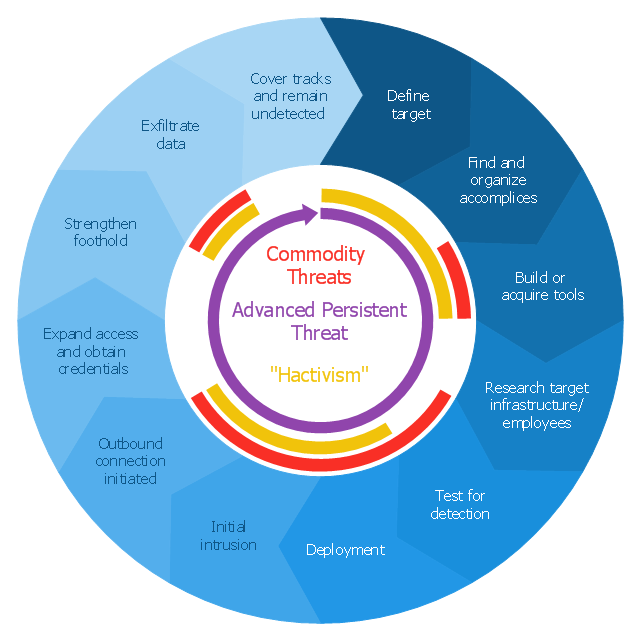
This circular arrows diagram sample shows advanced persistent threat lifecycle.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
It was designed on the base of the Wikimedia Commons file: Advanced persistent threat lifecycle.jpg.
[commons.wikimedia.org/ wiki/ File:Advanced_ persistent_ threat_ lifecycle.jpg]
This file is licensed under the Creative Commons Attribution-Share Alike 3.0 Unported license. [creativecommons.org/ licenses/ by-sa/ 3.0/ deed.en]
"Advanced Persistent Threat (APT) APT is a set of stealthy and continuous hacking processes often orchestrated by human targeting a specific entity. APT usually targets organizations and or nations for business or political motives. APT processes require high degree of covertness over a long period of time. As the name implies, APT consists of three major components/ processes: advanced, persistent, and threat. The advanced process signifies sophisticated techniques using malware to exploit vulnerabilities in systems. The persistent process suggests that an external command and control is continuously monitoring and extracting data off a specific target. The threat process indicates human involvement in orchestrating the attack.
APT usually refers to a group, such as a government, with both the capability and the intent to persistently and effectively target a specific entity. The term is commonly used to refer to cyber threats, in particular that of Internet-enabled espionage using a variety of intelligence gathering techniques to access sensitive information, but applies equally to other threats such as that of traditional espionage or attack. Other recognized attack vectors include infected media, supply chain compromise, and social engineering. Individuals, such as an individual hacker, are not usually referred to as an APT as they rarely have the resources to be both advanced and persistent even if they are intent on gaining access to, or attacking, a specific target." [Advanced persistent threat. Wikipedia]
The arrow donut chart example
"Advanced persistent threat lifecycle" was created using the ConceptDraw PRO diagramming and vector drawing software extended with the Circular Arrows Diagrams solution from the area "What is a Diagram" of ConceptDraw Solution Park.
 SWOT and TOWS Matrix Diagrams
SWOT and TOWS Matrix Diagrams
SWOT and TOWS Matrix Diagrams solution extends ConceptDraw PRO and ConceptDraw MINDMAP software with features, templates, samples and libraries of vector stencils for drawing SWOT and TOWS analysis matrices and mind maps.
 SWOT Analysis
SWOT Analysis
SWOT and TOWS Matrix Diagrams solution extends ConceptDraw PRO and ConceptDraw MINDMAP software with features, templates, samples and libraries of vector stencils for drawing SWOT and TOWS analysis matrices and mind maps.
- Swot Analysis Threat Examples
- Swot Examples Of Threats
- Ansoff's product / market matrix | SWOT analysis matrix diagram ...
- Threats In Swot Analysis Example
- Example Of Threats In Business
- Company Threats Examples
- Opportunities Threats Example
- Swot Example What To Put In
- Sample Business Analysis
- SWOT Analysis | Mind Maps for Business - SWOT Analysis | SWOT ...
- SWOT Analysis | SWOT analysis for a small independent bookstore ...
- External Threats Diagram
- Strengths Weaknesses Opportunities And Threats Example
- Example Of Threats Of A Person
- Examples Of Threats And Opportunities For A Business A Bookshop
- Export Company Swot Template
- Examples Of Opportunities And Threats Of A Student
- Swot Analysis Personal Development Plan Example
- Strength Weakness Opportunities Threats Examples
- Marketing | SWOT Analysis | Venn Diagram Examples for Problem ...